This post summarzie as a Tenable Vulnerability Management Specialist, what you should know, such as installation and configuration, operations, a technology overview including architecture and design discussions for typical environments, and detailed scanning and analysis instructions.
Host Discovery
Default host discovery Template Good For:
- Great starting point
- Quickly identifies assets for running VA (vulnerability assessment) only on live targets
- Minimal network impact
Best Practice
- daily – run scan on the network to discover new hosts
- use scan scheduling to automatically discover assets
- do not scan through firewall
- if icmp is not disabled on network devices, a discovery scan can cause false positives and other issues
- If has to scan through firewall
- ensure firewall is correctly configured to allow Scanner
- Disable ICMP in Discovery scan
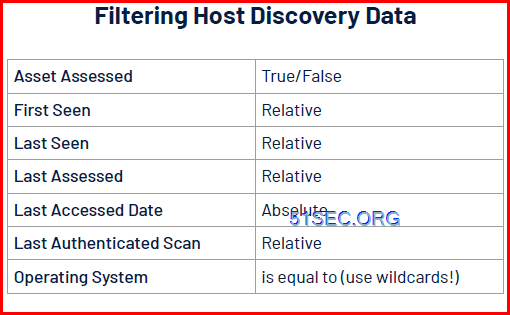
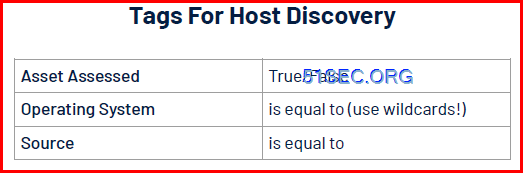
Host Discovery Options
- customize host discovery scans based upon network need
- Configurate a host discovery scan to perform OS identitifation and port scanning
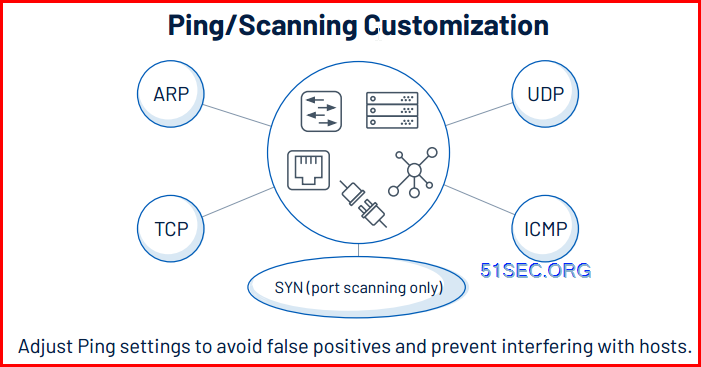
- Ping/scanning customization: Adjust Ping settings to avoid false positives and prevent interfering with hosts
- Tune a scan to improve performance
- For port scan tuning, if it is for speed, choose only SYN, leave TCP and UDP disabled.
- based on scanner’s hardware resources, tune Advanced-Max simultaneous checks (various options) for speed, accuracy and thoroughness
- Nessus Global Scan settings – Nessus Scanner settings can impact performance
Analysis
- Port scanner information
- Details about the Nessus scanner used
- more
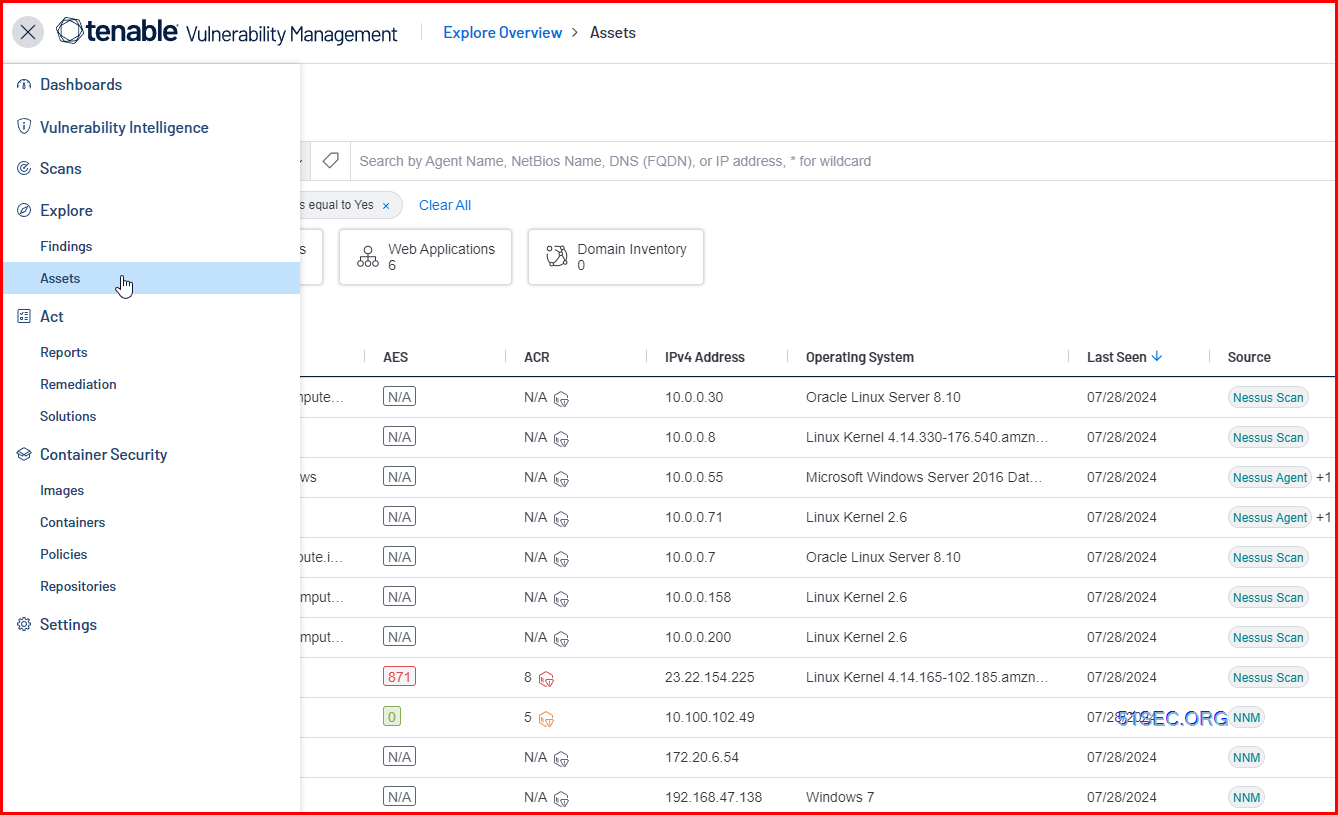
Alternative Host Discovery – Tenable Nessus Network Monitor (NNM)
Main Steps:
- Deploy Tenable Nessus Scanner (Internal) or Cloud Scanner (Public IP)
- Policy : Discovery Scan
- Scan targets
- Scan schedule (Optional)
Vulnerability Assessment
A comparison between “Basic Network Scan” and “Advanced Scan”
Settings |
Basic Network Scan |
Advanced Scan |
| Allows plugins to be enabled or disabled | No | Yes |
| Allows audits to be added to the scan | No | Yes |
| Default Max simultaneous hosts per scan | 30 | 5 |
| Default Network Timeout | 5 | 5 |
| Default Simultaneous checks per hosts | 4 | 5 |
| Default Port scan range | Common ports | Default ports |
| Default CGI scanning | Disabled | Disabled |
| Default methods for Host Discovery |
|
|
| Default Paranoina level (a.k.a. Override normal accuracy) |
Normal | Normal |
Credentialed Scans vs. Non-Credentialed
- Credentialed Scan (internal misconfigurations and hidden vulnerabilities)
- Non-Credentialed Network Scan (external details and externallyviewable vulnerabilities only)
Table 1: Summary of capabilities between Web Application Scanning and legacy Nessus WAS scans.
Features |
Web Application Scanning |
Legacy Nessus WAS |
| VM & WAS Unified Visibility | Yes | - |
| Safe Scanning | Yes | - |
| Advanced Authentication | Yes | No |
| Manual Crawling | Yes | No |
| OWASP Top 10 Project Support | Yes | No |
| Known Vulnerability Detection | - | Yes |
| Unknown Vulnerability Detection | Yes | - |
| Modern Framework Support | Yes | No |
| High Detection Accuracy | Yes | - |
Table 2: Details of capabilities between Web Application Scanning and legacy Nessus WAS
Features |
Web Application Scanning |
Legacy Nessus WAS |
| VM & WAS Unified Visibility | Web application assets are integrated with the same dashboards as other assets automatically for unified visibility. | Web application assets can be integrated into Tenable.sc by creating additional filters to customize the dashboard. |
| Safe Scanning | Users can create a list of blocked URLs to exclude from scans and define customized scan performance thresholds to avoid application disruption. | Users need to define customized scan performance thresholds to avoid application disruption. |
| Advanced Authentication | Supports a broad range of authentication options such as forms, cookies, NTLM, and Selenium scripts to address most web application requirements. Automatically detect when authentication is required and validate when authentication has been successfully configured. | Supports only login forms and cookie-based authentication. The product is unable to automatically detect or validate successful authentication. |
| Manual Crawling | Records manual crawling of web applications using Selenium to assess and validate user-defined workflows. This is an important capability for assessing Single Page Applications. | Manual crawling is not available. |
| OWASP Top 10 Project Support | The product is purpose-built for the OWASP Top 10 and provides out-of-the-box vulnerability assessment and reporting aligned to OWASP risk categories. | OWASP Top 10 is not supported out-of-the-box. Users can create custom dashboards to manually align specific vulnerabilities to OWASP risk categories. |
| Known Vulnerability Detection | Detects known or specified vulnerabilities related to Content Management Systems (WordPress, Joomla!, And Drupal). CVE plugins supporting web application servers, language engines, web frameworks, and JavaScript libraries are also available. | Supports a leading range of known or specified vulnerabilities based on CVE plugins. |
| Unknown Vulnerability Detection | Detects unknown or generic vulnerabilities in support of OWASP Top 10 without the need for specific CVE plugins. | Provides detection of generic cross-site scripting and injection vulnerabilities in support of OWASP Top 10. |
| Modern Framework Support | Supports web applications built with modern web frameworks such as HTML5, JavaScript, AJAX, and Single Page Applications, as well as traditional web frameworks. | Modern web framework support is not available. |
| High Detection Accuracy | Leading vulnerability detection accuracy with minimal false positives and negatives across all web applications. | Strong vulnerability detection accuracy across web applications built using traditional frameworks. |
Best Practice
- Credentialed scanning (with credential vaults if possible) should be performed whenever possible
- Credentialed vulnerability scans should be performed at least weekly, and more often if possible
- Basic Network Scan policy with credentials; weekly or more frequently
Advanced Network Scan Discovery Options
Advanced Network Scan – Assessment Options
Advanced Network Scan Policy – Reporting and Advanced Options
- Some vulnerabilities require that the scan actually launches a potentially harmful payload at the target.
- ACT_DESTRUCTIVE_ATTACK
- ACT_DENIAL
- ACT_KILL_HOST
- ACT_FLOOD
What is a Plugin?
Compliance Assessment
Custom Audit File Creation
Compliance Assessment – Analysis
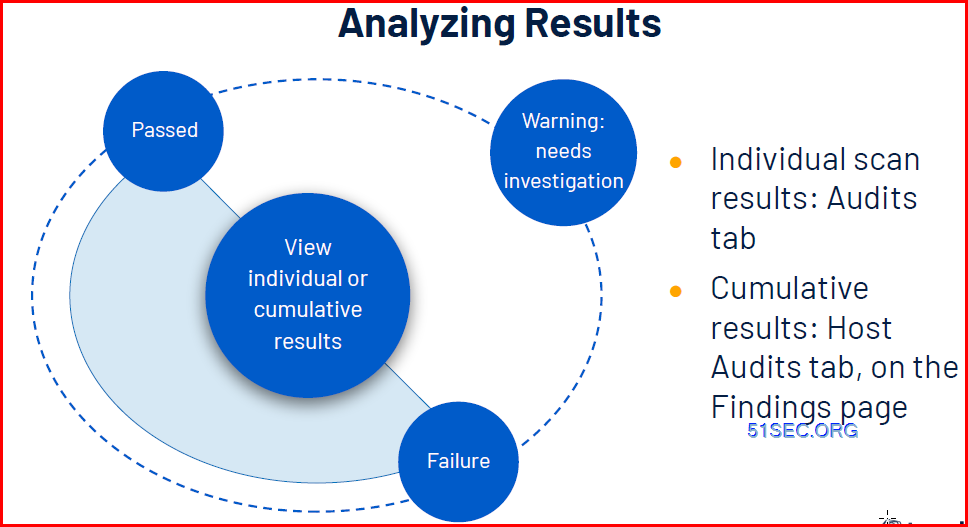
Vulnerability Analysis
- ⅔ of all vulnerabilities are high or critical
- Many vulnerabilities are unlikely to be exploited
- No real analysis of business impact
- All assets are identical
- Threat recency
- Threat intensity
- Exploit code maturity
- Age of vulnerability (newer is more likely)
- Product coverage
- Threat sources
- + CVSS v3 impact score
Threat
- Recency — How recently have there been attacks utilizing this vulnerability?
- Intensity — Number and frequency of recent events (very low to very high)
- Sources — What data was used?
Exploit Code Maturity
- Parallels CVSS: Unproven → High
Product Coverage
- Number of unique products: Low → Very High
- Availability
- Integrity
- Confidentiality
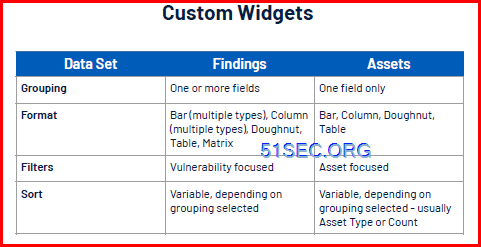
Dashboard
Reports
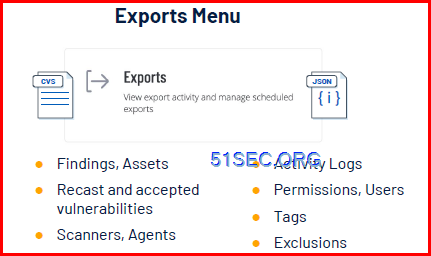
Exports
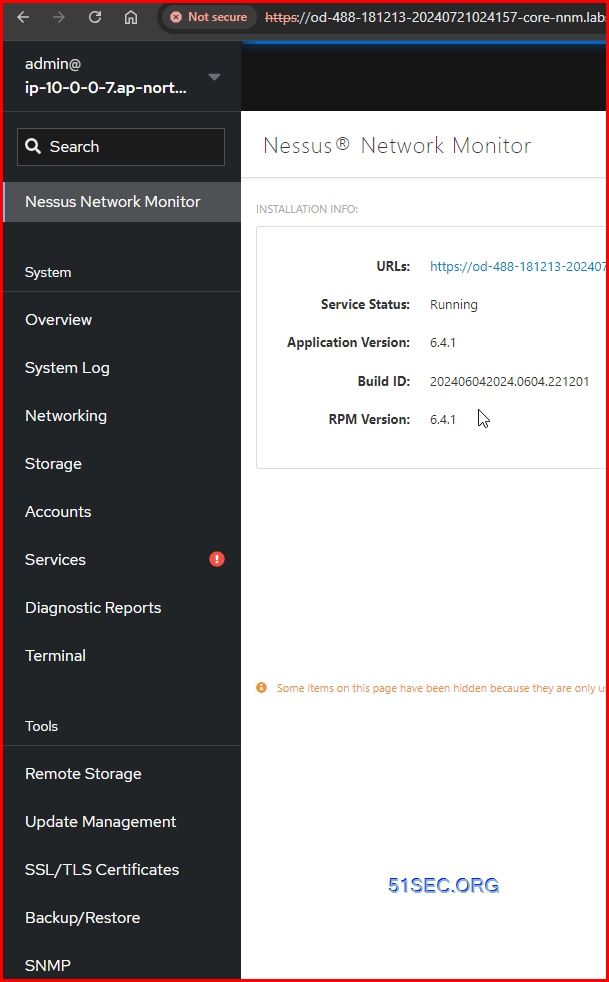
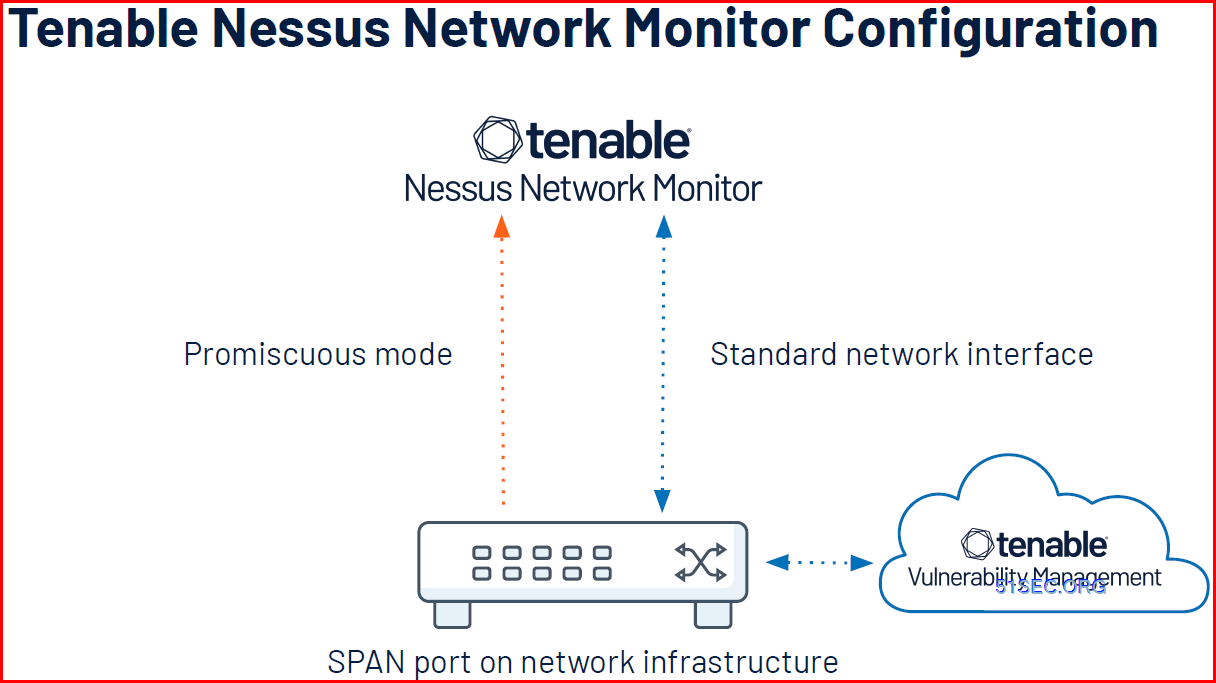
TenableCore Tenable NNM – Nessus Network Monitor
Tenable Nessus Network Monitor (NNM) – Schedule: Automatic
- Operates 24×7
- Requires access to a SPAN/mirror port for data
- Scans network traffic for cyber risk data
- Two operational modes: Host Discovery or Full
Tenable Nessus Network Monitor Installation
What is Tenable Nessus Network Monitor?
● Tenable Nessus Network Monitor is limited to monitoring 1 Gbps
● Can be licensed at an additional cost for 10 Gbps operations (high performance)
NNM Installation
- RHEL, Windows and other operating systems
- Install using the appropriate package manager.
- Tenable Core + NNM is also available
- Install on virtual platforms.
NNM Configuration:
- Connect to NNM using a web browser on port 8835 (https)
- Sign in with username “admin” and password “admin”
- Reset password
- Use “Cloud” as activation code
- Provide linking key
- Give scanner a name
- Select Network Interface
- Provide managed range
- Set exclusion range(s) – optional
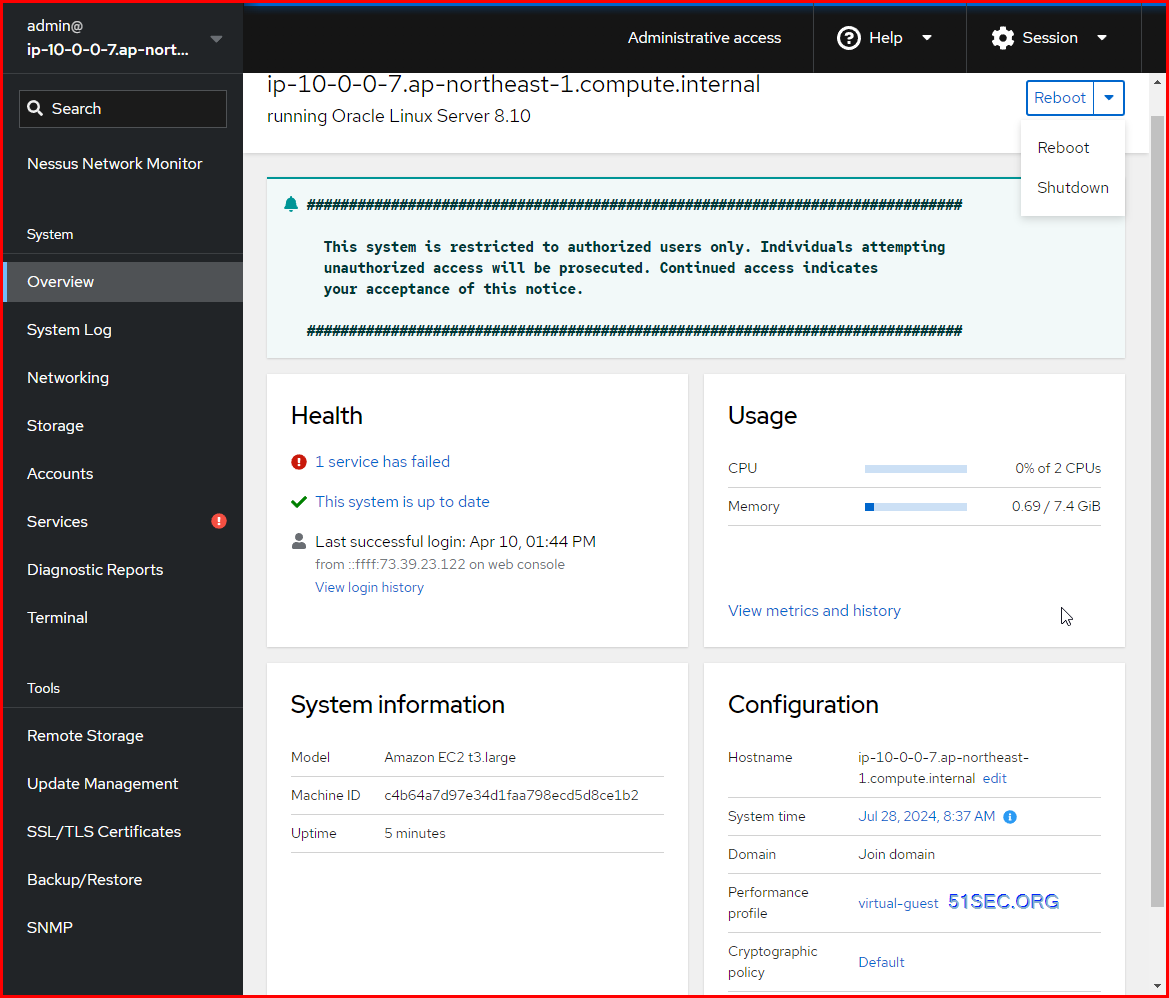
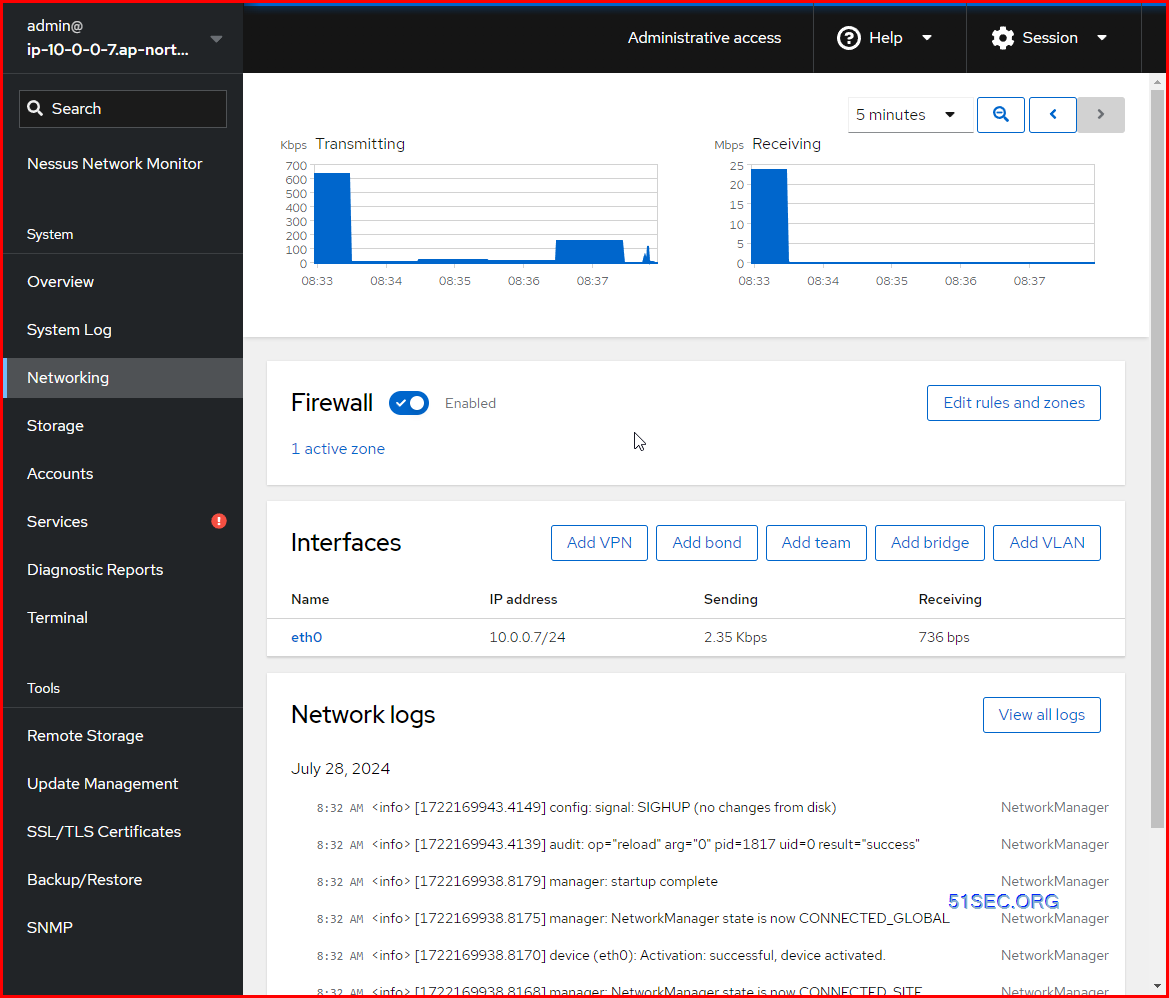
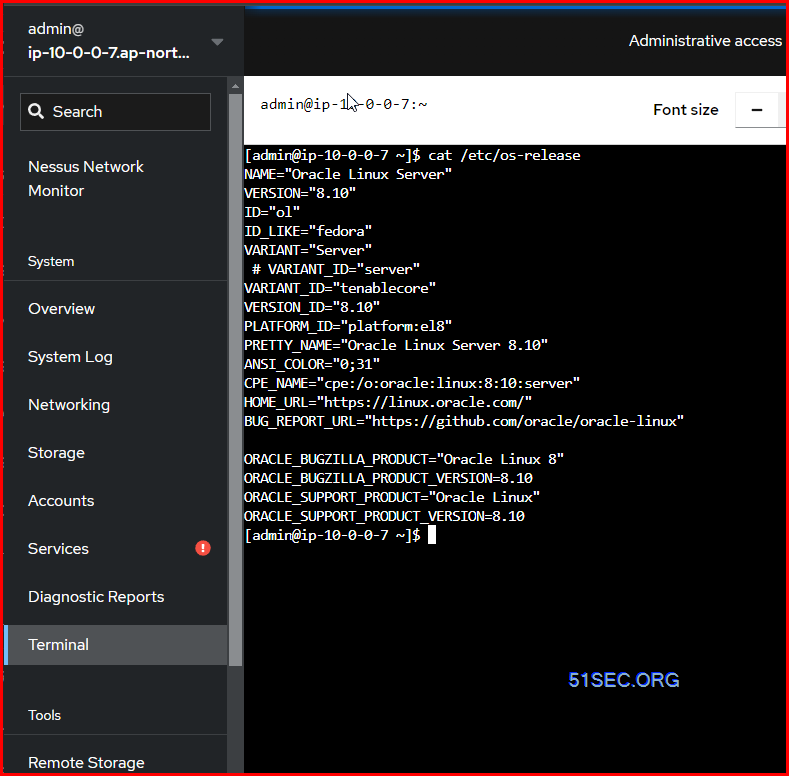
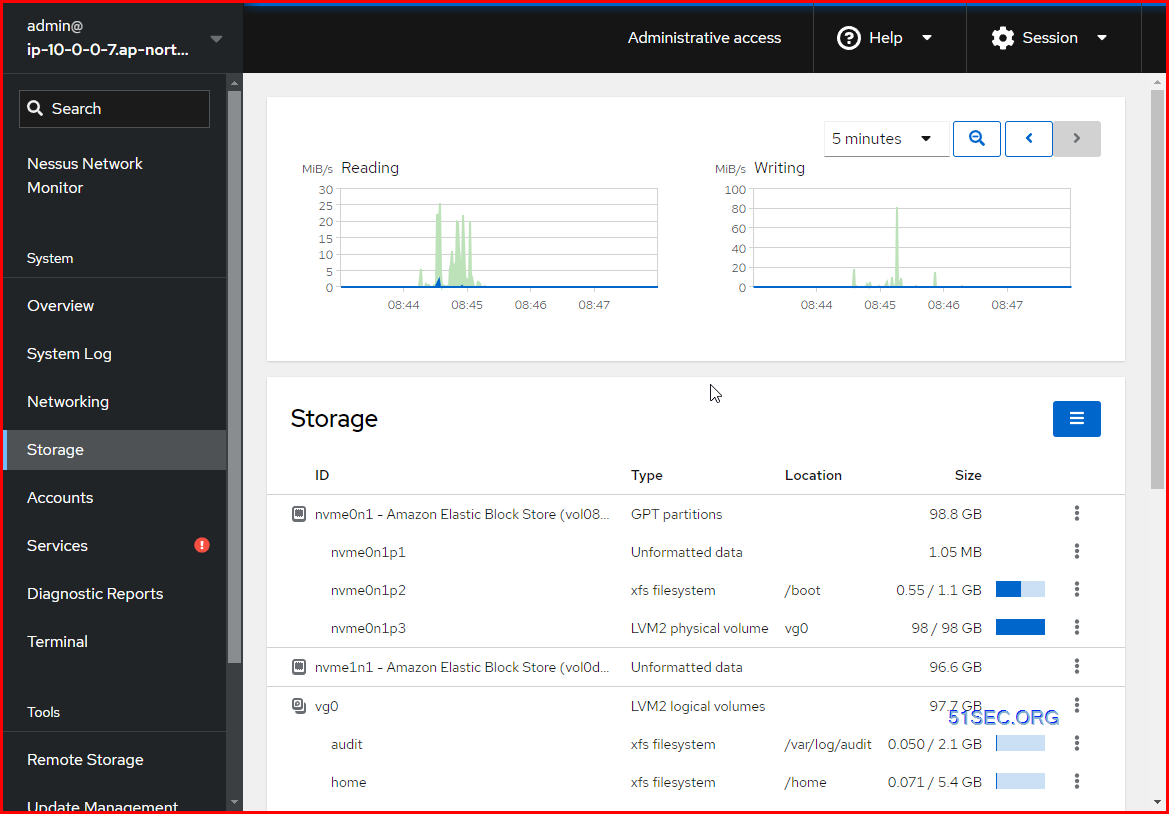
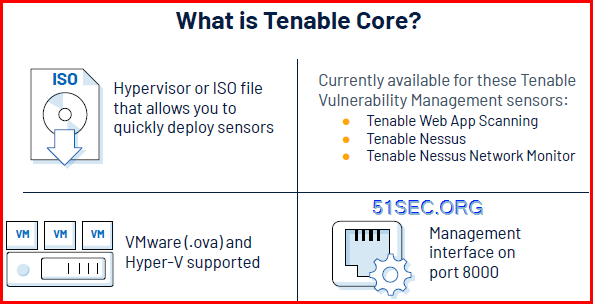
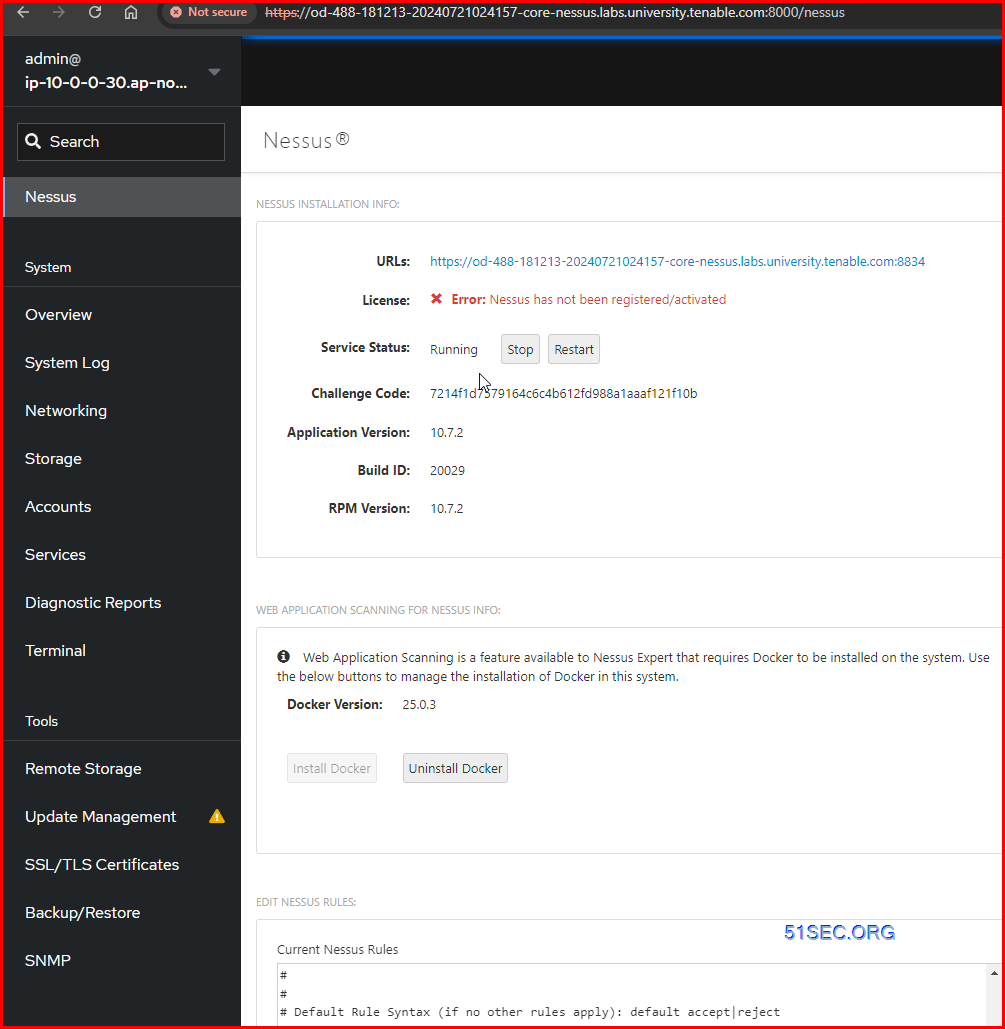
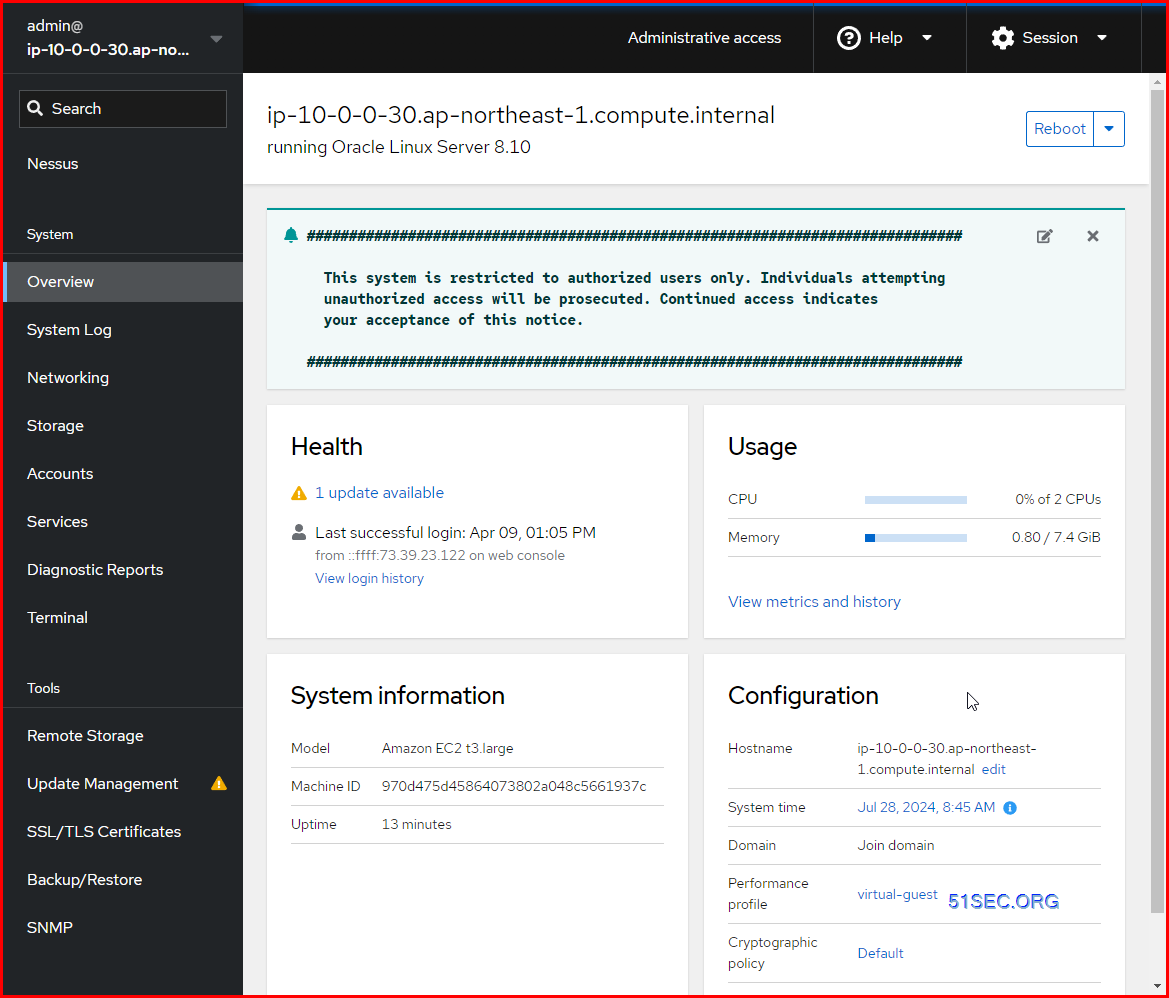
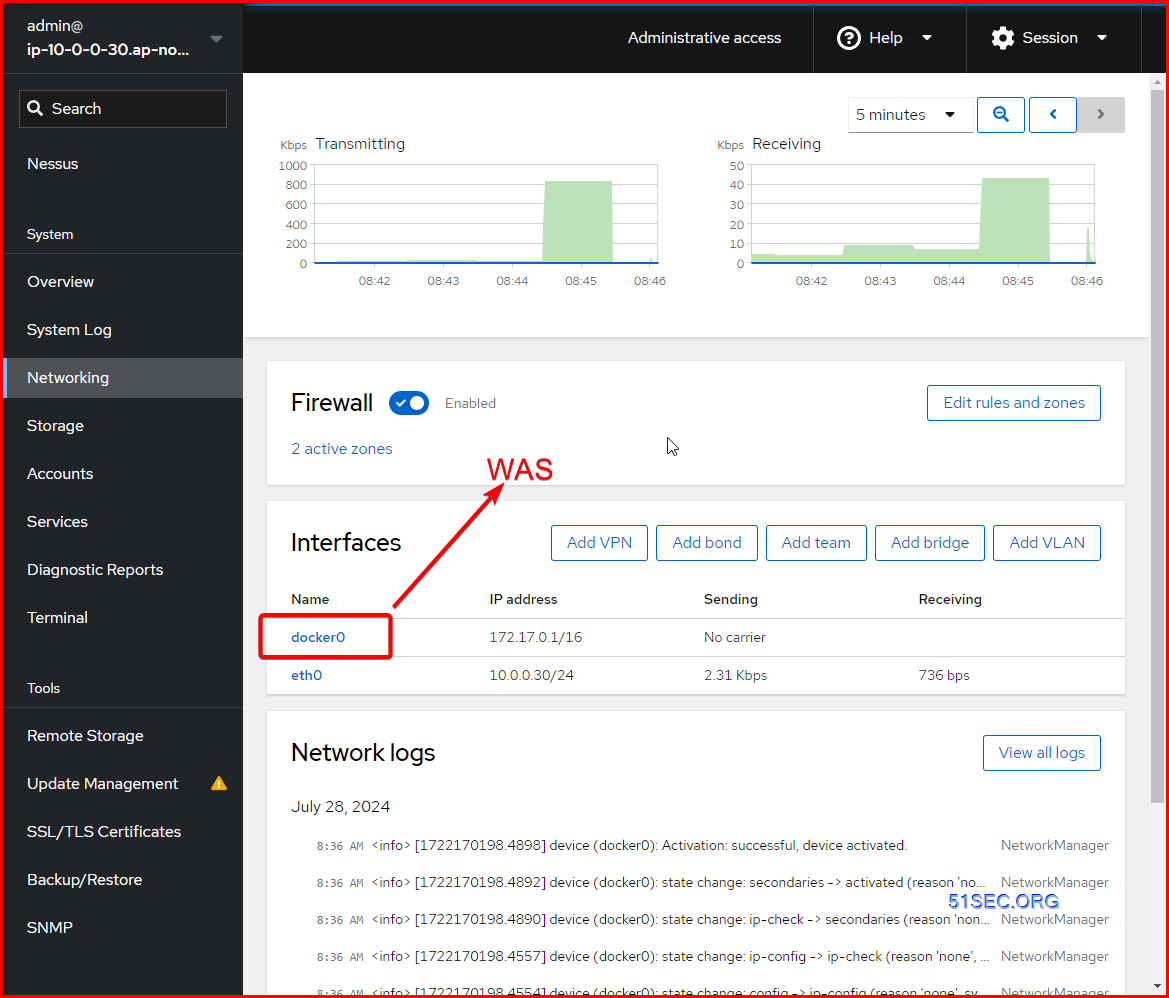
Tenable Core
You can use the Tenable Core operating system to run an instance of Tenable Nessus in your environment. After you deploy Tenable Core + Tenable Nessus, you can monitor and manage your Tenable Nessus processes through the secure Tenable Core platform.
Core Considerations
Deployment Process
1. Download image
2. Install (ISO or virtual image)
3. Connect to core using web browser on port 8000
4. Initial username and password: wizard/admin
5. Create admin account
6. Continue with sensor configuration
To deploy Tenable Core + Tenable Nessus as a VMware virtual machine:
-
Download the Tenable Core Nessus VMware Image file from the Tenable Downloads page.
- Open your VMware virtual machine in the hypervisor.
- Import the Tenable Core + Tenable Nessus VMware .ova file from your computer to your virtual machine. For information about how to import a .ova file to your virtual machine, see the VMware documentation.
- In the setup prompt, configure the virtual machine to meet your organization’s storage needs and requirements, and those described in System and License Requirements.
-
Launch your Tenable Core + Tenable Nessus instance.
The virtual machine boot process appears in a terminal window.
Core Interface
- Operating System (OS) level configuration Networking + storage + updates
- Start and stop sensor
- Command line access
- Resource utilization
Certificates can be installed using the Management interface.
Tenable Nessus
Traditional Tenable Nessus application installed on OS that you manage : For scanning private IPs
Tenable Cloud Scanner : Managed by Tenable For scanning public-facing IPs
- Connect to Nessus scanner using a web browser on port 8834 (https).
- On the Welcome screen, select “Managed by.”
- Select “Tenable.io” and provide the linking key.
- Create a username and password.
- Sign into Tenable Nessus to confirm username and password work.
Agents
How an Agent Works
Summary
● A linking key is needed to install the agent and connect it to Tenable Vulnerability Management.
● After installation, agents need to be placed into an Agent Group prior to assessment.
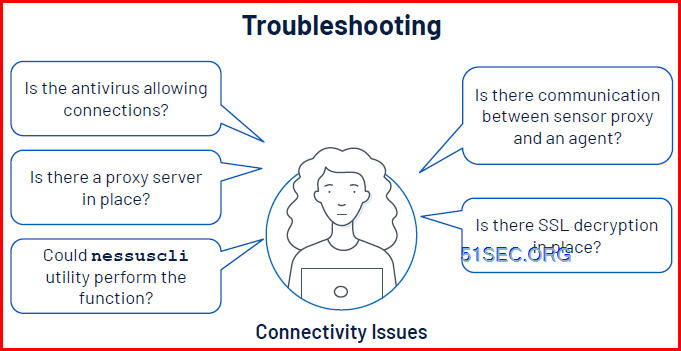
Possible Scanning Challenges
- Lack of reliability in network infrastructure
- Large number of assets in a network partition
- Active assessment is mission critical
- Scanners difficult to identify when configuring scans
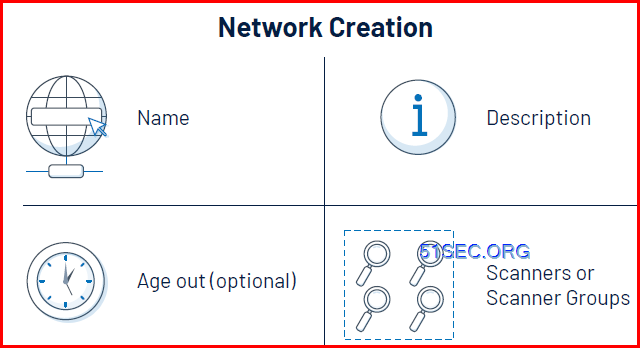
The Challenge of Crossover IP
Age Out Option
When To Use Networks
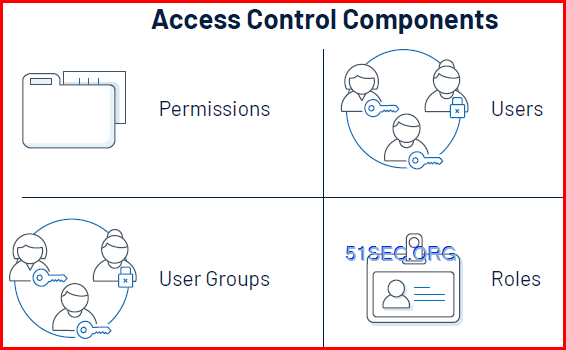
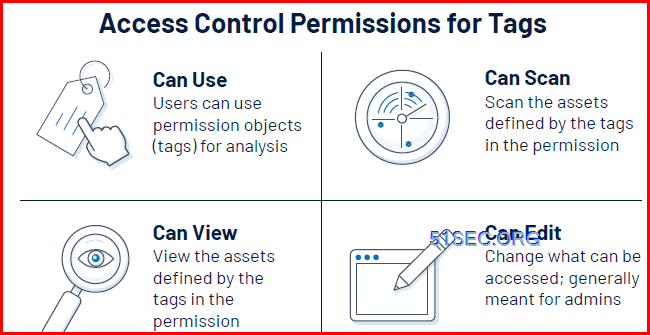
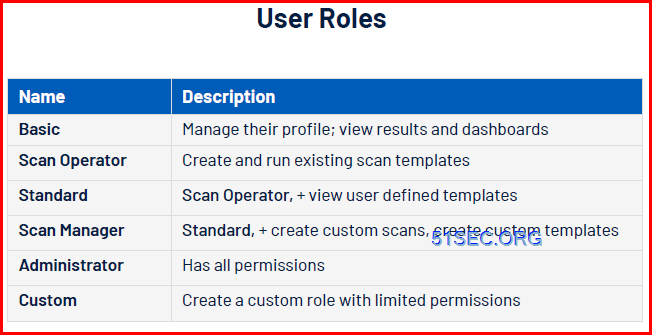
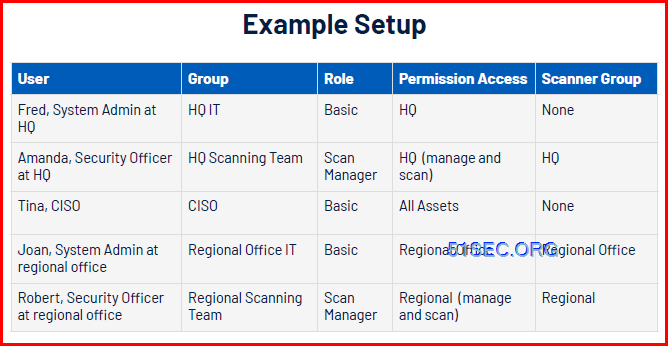
Access Control Components
The Importance of Access Control
● Improve overall security posture
● Simplify use of Tenable Vulnerability Management
● Improve reporting
● Reduce overall risk of internal threat
Setting Up Permissions with Tags
Object User Permissions
- Access to functions
- Access to assets
- Access to objects
- Scanner Group
- Agent Group
- Managed Credential
- Scan
References
- What are the differences between the “Basic Network Scan” and “Advanced Scan”
- What’s the difference between Web Application Scanning and Nessus Legacy WAS?
- Troubleshooting credentialed scanning on Windows
What ports are required for Tenable products? - How to check the SSL/TLS Cipher Suites in Linux and Windows
- Useful plugins to troubleshoot credential scans
Free:
- www.tenable.com/webinars
- youtube.com/TenableProductEducation
- community.tenable.com
- university.tenable.com
- docs.tenable.com
[…] Tenable Vulnerability Management Specialist – Discovery, Assessment, Analysis, Compliance, Dashbo… […]