This post is to record Tenable VM Lab information for future reference.
Run lab connectivity test
Use your web browser to connect to https://lab-test.labs.university.tenable.com/ .
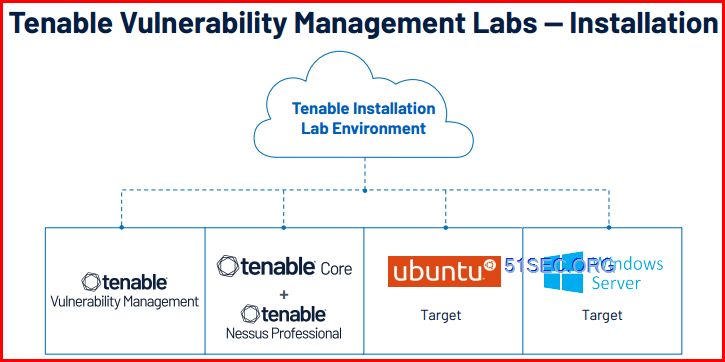
Topology:
Related posts:
Custom Dashboards
Lab Exercise 21: Custom Dashboards
At the end of this exercise, you will be able to:
● Add and edit dashboard templates
● Create a dashboard with various elements
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Vulnerability Management icon in the workspace.
3. Click the Menu button (𝄘) in the upper left corner, and select Dashboards .
4. Click +New Dashboard and select Template Library .
5. Click in the Search Templates (at the top) fi type security management and press <Enter> .
6. Hover over the dashboard Security Management Summary (Explore) and click +Add .
7. Hover over Copy of Security Management Summary (Explore) and click View .
a. Note: If a pop-up box appears titled Share a Dashboard , click Dismiss .
8. Click the More drop-down located at the top right and select Edit Dashboard .
9. Hover over the title Copy of Security Management Summary (Explore) and click the Edit (pencil) icon.
10. Delete Copy of , and add {yourname-} so that the Dashboard name is {yourname}- Security
Management Summary (Explore) .
11. Click the check mark .
a. Note: Once you have completed the challenge questions below, click Done Editing (at the
bottom) .
Part 1: Task 2 – Add a Widget to Pre-Existing Dashboard
Add templated widgets to an existing dashboard template.
Step-by-step Instructions:
1. Click Menu (𝄘), and then select Dashboards .
2. Hover over {yourname}- Security Management Summary (Explore) and click View .
3. Click the More drop-down and select Edit Dashboard .
4. Click +Add Widgets and select Template Widget .
5. Type CVSS Vulnerability in the Search Widgets fi and press <Enter> .
6. Hover over CVSS Vulnerability Counts Per Port (Explore) and click +Add .
7. Click Back to Dashboard located at the top right.
8. Click and drag the widget CVSS Vulnerability Counts Per Port (Explore) to the right of Most Commonly
Attacked Ports .
a. Note: As you move the cursor across the widget, look for the Move cursor icon to appear across
the title, and then click and drag.
9. Click Done Editing .
Part 2 – Create a Custom Dashboard and Widgets
In this section, create a custom dashboard and custom widgets.
Part 2: Task 1 – Create a Blank Dashboard
Create a blank dashboard named “{yourname}’s dashboard”.
Step-by-step Instructions:
1. Click Menu , and then select Dashboards .
2. Click +New Dashboard and select Custom Dashboard .
3. Hover over the title where the current date is displayed in the upper left corner, and click the Edit
(pencil) icon.
4. Rename the title in the fi with {yourname}’s dashboard (use your name or initials), and then click the
check mark .
5. Click Done Editing .
Part 2: Task 2 – Create a Custom Widget of a List of VPR 9 or Higher Vulnerabilities in HQ
Create a table of VPR 9 or higher items in HQ (10.0.0.0/24) by CVE.
Step-by-step Instructions:
1. Click Menu , and then select Dashboards .
2. Hove r over {yourname}’s Dashb oard and click View .
3. Click the More drop-down and select Edit Dashboard .
4. Click +Add Widgets and select New Custom Widget .
5. Locate the General section, click the Chart Type drop-down, and then select Table .
6. Type VPR 9 or Higher CVEs in HQ in the Name fi .
7. Locate the Data section, and ensure the Data Set drop-down displays Findings . If it does not, choose it from the drop-down list.
8. Ensure the Entity drop-down displays Vulnerabilities . If it does not, choose it from the drop-down list.
9. Delete Severity from the Group By drop-down by clicking the X. Then, click on Select , and select CVE instead.
10. Select Count from the Sort Fields drop-down.
11. Click Select Filters .
12. Click Find Filters , type VPR in the Search fi and then select VPR .
13. Close the Select Filters box by clicking the X.
14. Click on VPR: is equal to to edit the VPR filter
15. Click on is equal to, and instead select is greater than or equal to .
16. Type 9 in the next field
17. Click Save .
18. Click Update Preview located at the bottom right.
19. Click Save and Exit .
20. Locate the VPR 9 or Higher CVEs in HQ widget and click the More button ( ⠇) to the right of it .
21. Select Configure .
a. Note: The panel on the right will expand.
22. Click the Select Filter Type drop-down and select Custom .
23. Enter 10.0.0.0/24 in the Enter IP Addresses, Ranges, CIDRS, or Hostnames fi and, then click Apply .
24. Click Done Editing .
Part 2: Task 3 – Create a Bar Chart
Create a bar chart of vulnerability counts for the top fi vulnerable assets in HQ with critical vulnerabilities.
Step-by-step Instructions:
1. Click Menu , and then select Dashboards .
2. Hover over yourname’s Dashboard and click View .
3. Click the More drop-down and select Edit Dashboard .
4. Click +Add Widgets and select New Custom Widget
5. Locate the General section, click the Chart Type drop-down, and then select Bar .
6. Type Vuln counts in HQ in the Name fi .
7. Locate the Data section, and ensure the Data Set drop-down displays Findings . If it does not, choose it
from the drop-down list.
8. Ensure the Entity drop-down displays Vulnerabilities . If it does not, choose it from the drop-down list.
9. Delete Severity from the Group By drop-down by clicking the X. Then, click on Select , and select Asset
name instead.
10. Select Count from the Sort Fields drop-down.
11. Click Select Filters .
12. Click Find Filters , type ip in the Search fi and then select IPv4 Address .
13. Clear the Search fi and type severity.
14. Select Severity .
15. Close the Select Filters box by clicking the X.
16. Click IPv4 Address: is equal to “” .
17. Type 10.0.0.0/24 in the fi underneath is equal to .
18. Click Save .
19. Click Severity:is equal to .
20. Select Critical , and then click Save .
21. Click Update Preview .
a. Note: Answer the challenge questions below, and then continue with the remaining steps.
22. Click Save and Exit .
23. Click Done Editing .
Answer Key
Part 1: Task 1
1. Can you change a widget to report on a specific IP range?
● Yes. Click the More icon (three vertical dots) in the upper right of the widget. Then, under Select
Actions, select Custom and provide the IP range.
2. How can you move a widget?
● Hover over a widget, click and drag it to its new location.
3. How can you delete a widget?
● Click the More icon (three vertical dots) in the upper right corner of a widget and select Delete.
Part 1: Task 2
1. Is there a way you can change the cells in the widget CVSS Vulnerability Counts per port?
● No.
2. What can you change with this widget?
● The assets the widget reports on, and the name.
Part 2: Task 1
1. Where did your new dashboard appear?
● Near the last Dashboard in the list.
2. How can you change this to be your default dashboard?
● Click the More icon (three vertical dots) in the upper right corner of the dashboard and select
Make Default.
3. If you make a dashboard a default dashboard, where does it appear on the list of dashboards?
● As the fi dashboard.
Part 2: Task 2
1. Is the table showing a list of CVEs?
● No.
2. What do you need to do to update the table?
● Click Update Preview.
3. Is the table sorted by severity? If not, how do you sort by severity?
● No. Change the Sort fi to Severity.
Part 2: Task 3
1. You have created two widgets for HQ with a fi of the IP range 10.0.0.0/24. Are there easier ways to
handle this?
● Yes, with tags or pre-saved fi
2. Is this chart showing all the hosts in 10.0.0.0/24? If not, which ones are being displayed?
● No, just the fi with the highest number of critical items.
Reports from Templates
Part 1 – Create and Launch a Report from a Template
In this part, create a report from a template, and then launch and download the report.
Part 1: Task 1 – Create a Report
Create a report for HQ assets, using the Vulnerabilities by Common Ports template.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Menu , locate the Act section, and then select Reports .
3. Click +Create New Report .
4. Hover over Vulnerability Management and click Select .
5. Select template Vulnerabilities by Common Ports (Explore) .
6. Click Generate Report.
7. Enter Vulnerabilities by Common Ports in the Name fi
8. Click Edit Filter (at the top).
a. Note: The panel on the right will expand.
9. Click the Select Filter Type drop-down, and select Tags .
10. Click the Select Tags drop-down, and select tag Regions:HQ .
11. Click Apply .
12. Click Save .
Part 1: Task 2 – Generate and Download your Report
Launch the report created in the previous task, and then download it once the report is completed.
Step-by-step Instructions:
1. Click Menu , locate the Act section, and then select Reports .
2. Click the More button ( ⠇) in the Actions columns of Vulnerabilities by Common Ports , and select
Generate Report .
3. Click Report Results (at the top).
4. Note the Status of your report. Wait for your report to complete (you may need to refresh the page).
5. Click the More button ( ⠇) in the Actions columns of Vulnerabilities by Common Ports once the Status is
Completed .
6. Select Download .
Answer Key
Part 1: Task 1
1. What other options exist for report fi
● All Assets, and Custom Assets (IP list, CIDR, or range).
2. Can you set a fi on an individual chapter?
● Yes
Part 1: Task 2
1. Can you schedule this report?
● Yes. There is a Schedule option in the Actions column of My Report Templates .
2. Is PDF the only format available?
● Yes. If you need CSV or JSON, you would instead need to create an export from either the
Explore >Findings or Explore >Assets menus.
Lab Exercise 23: Custom Reports
Custom Report
Part 1 – Create and Launch a Custom Report
Custom reports are a great tool to report on compliance benchmarks. In this section, create a custom report using
template widgets and chapters for CIS Windows Server 2016, and then launch and download the report.
Part 1: Task 1 – Create a Report
Create a formatted PDF report that details all of the CIS Compliance results from the Windows Server 2016
compliance scan that was run in a previous lab.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Menu , locate the Act section, and then select Reports .
3. Click +Create New Report .
4. Click +Create Custom Report .
5. Type CIS Windows Server 2016 Compliance Results in the Name fi
6. Hover over Add New Widget , and click Widget Library .
7. Type CIS Windows Server 2016 v in the search bar and press the Enter key.
8. Hover over CIS Windows Server 2016 v2.0.0 Checks by Audit File (Explore) , and click Add .
a. Note: The version number may update. Select the same version number of the audit that you
used in the Compliance Scans lab (Exercise 15).
9. Click Done .
10. Hover over Add New Chapter , and click Chapter Library .
11. Type CIS Windows Server 2016 v in the search bar and press Enter .
12. Hover over CIS Windows Server 2016 v2.0.0 (Explore) , and click Add .
a. Note: The version number may update. Select the same version number of the audit that you
used in the Compliance Scan lab.
13. Click Done .
Part 1: Task 2 – Generate and Download your Report
Launch the report created in the previous task, and then download it once the report is completed.
Step-by-step Instructions:
1. Click Menu , locate the Act section, and then select Reports .
2. Click the More button ( ⠇) in the Actions columns of CIS Windows Server 2016 Compliance Results , and
select Generate Report .
3. Click Report Results (at the top).
4. Note the Status of your report. Wait for your report to complete (you may need to refresh the page).
5. Click the More button ( ⠇) in the Actions columns of CIS Windows Server 2016 Compliance Results ,
once the Status is Completed .
6. Select Download .
Answer Key
Part 1: Task 1
1. How many widgets are available to add to a custom report?
● The exact number may vary, as Tenable regularly updates widgets. However, there should be
around 890 or more.
Part 1: Task 2
1. Can you protect this report with a password?
● Yes. There is an Email option in the Actions column of Report Results . There is an option to
enter a password in the email form.
Exports
Lab Exercise 24 : Exports
Part 1: Task 1 – Exporting a Dashboard
A dashboard can be exported as a report. Create and then export your newly created dashboard.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Select Dashboards from the menu located in the upper left corner.
3. Click New Dashboard , and then select Template Library .
4. Click in the Search Templates text bar at the top, and enter Quarterly VPR .
5. Select the Quarterly VPR Analysis (Explore) dashboard, and click Add .
6. Select Copy of Quarterly VPR Analysis (Explore) , and click View .
7. Click on Export and select PDF .
8. Wait for the export to fi then save it to your local computer. Open it with a PDF reader.
Part 1: Task 2 – Identify and Report on Assets
Generate a list of assets in the HQ network (10.0.0.0/24).
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click on Vulnerability Management .
3. Select Findings from the menu located in the upper left corner.
4. Click Asset next to Group By (at the top, just underneath the Filter icon).
5. Click on Advanced to the left of Saved Filters .
6. Click at the end of text in the Saved Filters fi and click AND . Then, select IPV4 ADDRESS .
7. Select Is equal to .
8. Type 10.0.0.0/24 and press Enter .
9. Select 19 Assets (the exact number may vary slightly in the lab environment) using the checkbox.
10. Click Export .
11. Change the Name to HQ Assets last 30 days .
12. Select CSV .
13. Enable the Schedule slider by clicking it.
14. Click the date and select tomorrow’s date .
15. Click the time , and select midnight .
16. Select your current Timezone .
17. Click Daily and select Weekly on {Day} .
18. Click Schedule Export .
Part 1: Task 1
1. Can this report be scheduled to run automatically? If so, how?
● Yes, by choosing Schedule instead of PDF .
2. Can this report be delivered automatically via email? Is it encrypted by default?
● Yes, it can be delivered automatically. No, it is not encrypted by default, but it can be.
Part 1: Task 2
1. When new assets are discovered in HQ, are they reported automatically?
● Yes
2. Where would you change this schedule?
● Navigate to Settings>Exports , and then click the Schedules tab.
Tenable Core
Lab Exercise 26: Tenable Core
Part 1 – Generate a Diagnostic Report in Tenable Core
In this section, if you are opening a trouble ticket with Tenable and believe there is a problem with Tenable Core, attach a diagnostic report to assist in researching the issue.
Part 1: Task 1 – Log in to Tenable Core + Nessus and Generate a Diagnostic Report
Log in to Tenable Core + Nessus and generate a diagnostic report.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click Limited Access (at the top).
3. Enter the administrative password (Tenable123456789! ), and click Authenticate .
4. Click Diagnostic Reports .
5. Click Run Report .
6. Type Full Diagnostic next to Report label , and click Run report .
a. Note: Wait for the report to fi generating. The progress percentage should appear at the
bottom of the pop-out box.
7. Click Download .
8. Save the fi
Part 2 – Adjust Update Options
Tenable Core has a variety of update options. In this section, view and change those options.
Part 2: Task 1 – Perform a Manual Update
Perform a manual update of Tenable Core + Nessus.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. If you are not already in administrative mode, click Limited Access (at the top), and enter the
administrative password (Tenable123456789! ), and click Authenticate .
a. If it says Administrative access at the top, you may skip this step.
3. Click Update Management .
4. Under Update Status , click the refresh icon to check for updates.
a. Note: There may be a warning at the top that a reboot is required to update packages found in a
previous update check. If you select the check box for “Reboot when fi the system may
not reboot if no newer updates are found. If this is the case:
i. Click Overview .
ii. Click the drop-down next to Reboot (at the top), and select Reboot .
iii. Click Reboot .
5. Wait a few minutes for the system to reboot. You may need to refresh your browser to log back in.
6. Log back in, and click Update Management again to answer the challenge questions.
a. If you are not already in administrative mode, click Limited Access (at the top), and enter the
administrative password (Tenable123456789! ), and click Authenticate .
i. If it says Administrative access at the top, you may skip this step.
Part 2: Task 2 – Set Periodic Updates
Tenable Core can be set to perform updates automatically on a schedule. Set Tenable Core to update at
08:00AM on Saturdays.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. If you are not already in administrative mode, click Limited Access (at the top), and enter the
administrative password (Tenable123456789! ), and click Authenticate .
a. If it says Administrative access at the top, you may skip this step.
3. Click Update Management .
4. Check the Unit State in the Scheduled System Updates section. If it says Enabled , leave it as it is.
Otherwise, click Edit and enable the toggle.
5. Click Edit on the Timer Config Line in the Scheduled System Updates section.
6. Enter Sat under Day of Week .
7. Enter * under Day of Month .
8. Enter 08 under Hour .
9. Enter 00 under Minute .
10. Click Save .
Part 2: Task 3 – Set Updates to Run on Startup
Configure updates to run at startup.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click Update Management .
3. Locate the On-boot System Updates section. If the Unit State is enabled , then you can continue.
Otherwise, click Edit, and enable the toggle.
Part 3 – Enabling SNMP
SNMP is a useful protocol for retrieving information about hosts without logging in to them.
Part 3: Task 1 – Install the SNMP Service
Install the SNMP service on Tenable Core + Nessus.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. If you are not already in administrative mode, click Limited Access (at the top), and enter the
administrative password (Tenable123456789! ), and click Authenticate . If it says Administrative access
at the top, you may skip this step.
3. Click SNMP . (The option is at the bottom of the page; you may need to scroll down)
4. Click Install SNMP .
5. Wait for the installation to fi
Part 3: Task 2 – Configure SNMPv3
Best practices call for using SNMPv3 whenever possible. Configure SNMPv3 so that it uses MD5 with read-only
credentials of user/readme12 and read-write credentials of admin/writeme12.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. If you are not already in administrative mode, click Limited Access (at the top), and enter the
administrative password (Tenable123456789! ), and click Authenticate . If it says Administrative access
at the top, you may skip this step.
3. Click SNMP .
4. Locate the line Read-only Hash Algorithm , in the SNMPv3 access control setup section. Click the
drop-down to the right and select MD5 .
5. Type user in the read-only access username fi
6. Type readme12 in the read-only access user password fi
7. Click the Read-write Hash algorithm drop-down and select MD5 .
8. Type admin in the read-write access username fi
9. Type writeme12 in the read-write access user password fi
10. Click Save Configuration .
Optional Advanced Problems
This section is optional and can be completed during any free time you may have available while taking this course.
TOTAL ESTIMATED OPTIONAL EXERCISE TIME: 5:00 MINUTES
Task 1 – Create a Credentialed Scan of Tenable Core using SNMPv3
Using Tenable Vulnerability Management, create a credentialed scan of 10.0.0.181 (Tenable Core + Nessus) using
SNMPv3 credentials and run the scan. Do not use Tenable Core + NNM.
Task 2 – Disable Automatic Updates
Some organizations have change management controls that disallow automatic updates. Disable all
automatic updating of Tenable Core + Nessus.
Task 3 – Enable SNMPv3 on Tenable Core + NNM
Login to Tenable Core + NNM, enable SNMPv3 and create credentials similar to what you did for Tenable Core
+ Nessus.
Answer Key
Part 1: Task 1
1. What is the extension of the fi that was generated?
● tar.gz
Part 2: Task 1
1. Is this system up-to-date?
● Yes
2. Is there a way to determine what was updated and when?
● Yes, the system update history shows dates and what was updated. You can fi this on the
Update Management page by scrolling down.
Part 2: Task 2
1. Click Update Management and look for the entry Next Run . Is it set to 08:00AM?
● No. Explanation: To prevent the Tenable servers from being fl with update requests, a
random number of minutes between 00 and 60 is added to the update schedule.
2. Go to the terminal and type date . What time zone is the Tenable Core set to?
● U.S. Eastern Time
Part 2: Task 3
1. Click Edit next to Unit State in On-boot System Updates . What service is used to update?
● dnf-automatic-install.service
Part 3: Task 1
1. Examine the interface. Does Tenable Core support SNMPv1?
● No
2. What versions of SNMP are supported in Tenable Core?
● 2c and 3
Part 3: Task 2
1. Did the snmpd service restart?
● Yes.
2. What other items might you want to consider configuring for SNMPv3 support?
● The common items of contact and location.
Nessus
Lab Exercise 27: Tenable Nessus Installation
Part 1 – Configure Nessus and Connect to Tenable Vulnerability Management
In this part, your Hypervisor Management team has deployed a Tenable Core + Nessus in their Headquarters and
performed the initial configuration. Now, connect it to Tenable Vulnerability Management.
Part 1: Task 1 – Log in to Tenable Vulnerability Management and Obtain the Linking Key
Log in to Tenable Vulnerability Management and retrieve the linking key.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu in the upper left corner, and select Settings .
4. Click Sensors located in the Scanning section.
5. Click + Add Nessus Scanner .
a. Note: DO NOT click Regenerate.
6. Click Copy to save the linking key to your clipboard.
7. Read the information in the rest of the window.
8. Click the X in the upper right corner to close the window.
9. Click Linked Scanners .
10. Open a text editor and paste the linking key. This way you can retrieve it later, in case you overwrite
what’s on your clipboard.
Part 1: Task 2 – Configure Tenable Nessus and Connect to Tenable Vulnerability Management
Log in to the management interface, connect to Nessus and use the linking key to perform initial
configuration.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click Nessus on the left side.
3. Right-click the link to the right of URLs and open the link in an incognito window (or InPrivate ,
depending upon your browser).
4. Accept the certificate. If using Google Chrome, and you cannot accept the certificate, type thisisunsafe
(anywhere in the browser window, as all one word).
5. Once you see the Welcome to Nessus screen, click Continue .
6. Select Link Nessus to another Tenable product .
7. Click Continue .
8. Select Tenable Vulnerability Management from the Managed by drop-down.
9. Paste the linking key in the fi under Linking Key .
10. Click Continue .
11. Type admin in the Username fi
12. Type Tenable123456789! in the Password field
13. Click Submit .
a. Note: Wait for Nessus to display Compiling plugins .
14. Log into Tenable Vulnerability Management via cloud.tenable.com with the credentials provided.
15. Click Menu and select Settings .
16. Click Sensors located in the Scanning section.
17. Click Linked Scanners .
18. Confirm the new Nessus scanner has been attached.
Part 2 – Check Status and Rename Scanner
In this section, using the nessuscli application on the command line, check the status of the link and change
the name of the scanner.
Part 2: Task 1 – Check the Status of the Link
Connect to the Nessus management interface on port 8000 and use the Terminal to check the link status.
Note: On a “non- Tenable Core” scanner, these same instructions can be used from the command line.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click Terminal .
3. Type sudo /opt/nessus/sbin/nessuscli managed status
4. Type Tenable123456789! when prompted for a password.
5. Confirm that the scanner is linked.
Part 2: Task 2 – Rename the Scanner
By default, when connecting to Tenable Vulnerability Management, the hostname is used for scanner names.
Using the command line, the name can be changed to something more descriptive. Unlink the scanner, then link it using the Name option. Note: On a “non- Tenable Core” scanner, these same instructions can be used from the command line.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click Terminal .
3. Type sudo /opt/nessus/sbin/nessuscli managed unlink
a. Note: If prompted for a password, type Tenable123456789!
4. Type sudo /opt/nessus/sbin/nessuscli managed link –key={your linking key}
–cloud –name={your-name}_Scanner_Added
a. Note: Your linking key is what you copied from Part 1 Task 1 Step 5. “Yourname” is your name.
Do not type the brackets or braces. Also, be sure to type in the command above: do not copy
and paste the entire command, as there may be formatting errors. (Using copy/paste for the
linking key is fi though.)
5. Type Tenable123456789! if prompted for a password.
6. Open a new browser window.
7. Log into Tenable Vulnerability Management via cloud.tenable.com with the credentials provided.
8. Click the Menu and select Settings .
9. Click Sensors located in the Scanning section.
10. Click Linked Scanners .
11. Confirm that you see a scanner with the name {your-name}_Scanner_Added .
Answer Key
Part 1: Task 2
1. What is the name of the scanner?
● Since you did not rename the scanner, the name of the scanner will default to the hostname of
the system hosting Nessus, in this case Tenable Core. It may appear as “ip-10-0-0-xxx(some
number).ca-central-1.compute.internal” (ca-central-1 will be replaced with a more local region
designation), or possibly “tenable-XXXXXX” (where XXXXXX is a random string).
2. What is the IP address of the scanner?
● 10.0.0.X (where X is some number). The IP address may vary, but will always be in the 10.X.X.X
range.
Part 2: Task 1
1. Are there currently any jobs pending?
● No.
2. On the command prompt, type sudo /opt/nessus/sbin/nessuscli to see a list of commands.
How would you create a bug report?
● sudo /opt/nessus/sbin/nessuscli bug-report-generator
Part 2: Task 2
1. What is the status of the newly re-linked scanner?
● This will either appear as “Oũine” or “Online.” It may take about 10 minutes for plugins to fully
compile before the Online status appears.
2. What platform is this scanner running on?
● Linux (es8-x86-64)
Tenable Nessus Network Monitor (NNM)
Part 1 – Install and Connect Tenable Nessus Network Monitor
In this part, install Tenable Nessus Network Monitor and connect it to Tenable Vulnerability Management.
Part 1: Task 1 – Log in to Tenable Vulnerability Management and Obtain the Linking Key
Log in to Tenable Vulnerability Management and obtain the linking key.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu in the upper left corner and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Nessus Network Monitors .
6. Click +Add Nessus Network Monitor .
7. Click Copy to save the linking key to your clipboard.
a. Note: DO NOT click Regenerate .
8. Read the information in the rest of the window.
9. Click the X in the upper right corner to close the window.
10. Open a text editor and paste the linking key.
Part 1: Task 2 – Configure NNM and Connect to Tenable Vulnerability Management
Log in to the management interface, connect to Nessus Network Monitor and perform initial configuration
using the linking key.
Step-by-step Instructions:
1. Log in to Tenable Core + NNM with the credentials provided.
2. Click Nessus Network Monitor on the left side.
3. Right-click the link to the right of URLs and open the link in an Incognito window (or InPrivate ,
depending upon your browser).
4. Accept the certificate. If using Google Chrome, and you cannot accept the certificate, type thisisunsafe
(anywhere in the browser window, as all one word).
5. Once you see the Nessus Network Monitor login screen, type admin in the Username fi
6. Type admin in the Password fi
7. Click Sign In To Continue .
8. Type Tenable123456789! in the Password fi when it prompts you for a new password.
9. Type Tenable123456789! in the Confirm Password fi
10. Click Next Step .
11. Type Cloud in the Activation Code fi
12. Paste in your linking key from the previous task in the Cloud Key fi
13. Type {yourname}-NNM in the NNM Name fi (Note: Do not use the brackets/braces.)
14. Click Next Step .
15. Select the eth0 (or ens5 ) box to the right of Monitored Network Interfaces .
16. Confirm that the Monitored Network Range is set to 10.0.0.0/24 .
17. Click Finish .
Answer Key
Part 1: Task 1
1. Compare this linking key with the one you used in the previous lab. Are they the same?
● Yes
2. What is the name of the current Nessus Network Monitor?
● Shared Nessus Network Monitor
Part 1: Task 2
1. When you performed the initial configuration, you set the Monitored Network Range to 10.0.0.0/24.
What would have happened if you had set it to 0.0.0.0/0?
● NNM would consider the entire internet “our network” and report on all IPs. This would very likely
exceed our license quickly. In addition, some internal vs. external threat analysis would not work
properly.
2. Log back in to Tenable Vulnerability Management and go to your list of Nessus Network Monitors. Does
it show the IP address of the NNM?
● Yes, this should display as 10.0.0.7. It may take a few minutes to appear.
3. What mode is NNM operating in?
● Asset Discovery Mode
Lab Exercise 29.2: NNM Configuration and Troubleshooting
Part 1 – Configure NNM for Full Analysis and Set the Frequency
By default, NNM runs in asset discovery mode. This will identify assets in your network, but will not identify
vulnerabilities. In this section, reconfigure NNM to analyze traŨc for vulnerabilities and update the reporting
frequency to every 15 minutes.
Part 1: Task 1 – Change NNM Settings to Perform Full Vulnerability Analysis
Configure NNM to perform full vulnerability analysis.
Step-by-step Instructions:
1. Log in to Tenable Core + NNM with the credentials provided.
2. Click Nessus Network Monitor on the left side.
3. Right-click the link to the right of URLs and open the link in an incognito window (or InPrivate , depending
upon your browser).
4. Accept the certificate. If using Google Chrome, and you cannot accept the certificate, type thisisunsafe
(anywhere in the browser window, as all one word).
5. Type admin in the Username fi
6. Type Tenable123456789! in the Password fi
7. Click Sign In to Continue .
8. Click the OK button, warning you that NNM is running in asset discovery mode.
9. Click the ⚙icon in the upper right corner and select Configuration .
10. Uncheck the box labeled Run in Discovery Mode.
11. Click Update .
Part 1: Task 2 – Set the Polling Frequency to Every 15 Minutes
By default, NNM connects to Tenable Vulnerability Management once per hour and checks for work and
updates. Change this to every 15 minutes by changing the polling value.
Step-by-step Instructions:
1. Log in to Tenable Core + NNM with the credentials provided.
2. Click Nessus Network Monitor on the left side.
3. Right-click the link to the right of URLs and open the link in an Incognito window .
4. Type admin in the Username fi
5. Type Tenable123456789! in the Password fi
6. Click Sign In to Continue .
a. Note: If not already in the Configuration menu:
i. Click the ⚙ icon in the upper right corner and select Configuration .
ii. Click Cloud Settings from the NNM Settings menu.
iii. Type 15 in the Polling Frequency fi
iv. Click Update .
Part 1: Task 3 – Set the Reporting Frequency to Every 15 Minutes
By default, Tenable Vulnerability Management asks for vulnerability data once per hour from NNM. Change
this by setting the Report Frequency value to 15 in Tenable Vulnerability Management.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu button, and select Settings .
3. Click Sensors located in the Scanning section.
4. Click Nessus Network Monitors .
5. Click {yourname}-NNM .
6. Click Settings .
7. Replace the contents of the Report Frequency (Minutes) fi with 15 .
8. Click Save .
Part 1: Task 1
1. Why might you want to run in Discovery Mode for some time before enabling full analysis?
● Discovery mode does not impact asset count. So, if you have misconfigured the managed range
so that it is too large, this will not impact your license.
2. Click Monitoring at the top. Do you see any vulnerabilities?
● Yes.
Part 1: Task 2
1. Go to docs.tenable.com and refer to the Nessus Network Monitor User Guide and fi the entry for
“Polling Frequency”, within the Cloud Settings section. Does this value set how often NNM collects data?
● No, this value sets how often NNM connects to Tenable Vulnerability Management and checks
for work.
2. Can you see the full linking key in the Settings window? If not, how would you fi it?
● No. Log into Tenable Vulnerability Management and go to the Sensors section under Settings .
Part 1: Task 3
1. Where can you view the NNM data from the new scanner?
● Either from Scans , or on the Findings page:
i. Select Scans from the main menu, and click on All Scans . Look for the scan named
{yourname}-NNM .
ii. All vulnerabilities are reported to the Explore >Findings page as well. Filter on “Source Is
Equal To NNM “. Note: This will report all Findings from ALL connected NNMs.
2. Where can you show past reports from NNM?
● In the History section of the Scans window for the NNM.
Agent
Part 1 – Install and Configure the Tenable Agent and Connect to Tenable
Vulnerability Management
Your Hypervisor Management team has deployed a Tenable Core + Nessus in Headquarters. In this section, install
the Agent on the host and connect it to Tenable Vulnerability Management.
Part 1: Task 1 – Log in to Tenable Vulnerability Management and Obtain the Linking Key
Log in to Tenable Vulnerability Management and obtain the linking key.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu in the upper left corner and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Nessus Agents .
6. Click +Add Nessus Agent .
7. Click Copy to save the linking key to your clipboard.
a. Note: DO NOT click Regenerate.
8. Read the information in the rest of the window.
9. Click the X to close the window.
10. Open a text editor and paste in the linking key.
Part 1: Task 2 – Install Agent and Connect to Tenable Vulnerability Management
Log in to the management interface on the Nessus Scanner, and use the Terminal to install the agent in the
/tmp directory. Note: For this lab, the Nessus Agent is already in the /tmp directory to simplify the process.
In a normal environment, you would download the agent from the Tenable website and upload it using Server
Message Block (SMB) for Windows, or Secure File Transfer Protocol (SFTP) for Linux/Unix.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Core + Nessus with the credentials provided.
2. Click terminal on the left side.
3. Type cd /opt
4. Type sudo rpm -ivh ./N and press the Tab key. (Tab is the autocomplete key for Linux hosts.)
Then, press Enter .
5. Type the same password you used in Step 1, when prompted for a password or the password for the
Tenable Core + Nessus .
6. Type sudo /opt/nessus_agent/sbin/nessuscli agent link –key={The linking
key that was obtained in Task 1} –cloud –name=”Tenable Nessus
Agent–{yourname}”
a. Note: Your linking key is what you copied from Part 1, Task 1, Step 5. “Yourname” is your name.
(Do not type the brackets or braces.)
7. Type sudo /bin/systemctl start nessusagent.service
8. Type sudo /opt/nessus_agent/sbin/nessuscli agent status
Part 2 – Create an Agent Group and Assign an Agent
In this section, create an agent group for Tenable Infrastructure so you can scan the infrastructure on an
appropriate schedule.
Part 2: Task 1 – Create an Agent Group
Create an agent group called Tenable Infrastructure in order to scan the Tenable infrastructure in one complete
scan.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Nessus Agents .
6. Click Agent Groups .
7. Click +Add Agent Group .
8. Type Tenable Infrastructure in the Group Name fi
9. Click Save .
Part 2: Task 2 – Assign the Tenable Nessus Agent to the Agent Group
Assign the Tenable Nessus Agent to the agent group.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Nessus Agents .
6. Click Agent Groups .
7. Click Tenable Infrastructure .
8. Click +Assign Agents .
9. Select Tenable Nessus Agent-{yourname} .
10. Click Assign .
Answer Key
Part 1: Task 1
1. Compare this linking key with the ones you used in the previous labs. Are they the same?
● Answer: Yes
2. How many agents are currently connected to Tenable Vulnerability Management?
● Answer: 2
Part 1: Task 2
1. What part of the output from Step 8 shows that the agent has been linked to Tenable Vulnerability
Management?
● Linked to: cloud.tenable.com:443. (If it says “connection has not been attempted,” wait two
minutes and try again.)
2. What part of the output from Step 8 indicates whether an agent is ready to scan? Is the agent ready to
scan?
● Plugin set. No, the agent has not downloaded a set of plugins.
Part 2: Task 1
1. Check the Tenable online documentation for nessuscli agent. Is there a way to add an agent group
from the command line instead of in Tenable Vulnerability Management?
● Yes, with the –groups parameter.
2. Type sudo /opt/nessus_agent/sbin/nessuscli agent status. Has the agent received a
set of plugins? If so, is there a way to tell when the plugins were updated?
● It should be yes (if not, wait a few minutes and retry). The line Plugin Set shows the date of the
plugin update, in the format YYYYMMDD.
Part 2: Task 2
1. Go back to the list of agents. Is there a way to list which agents are a member of the Tenable
Infrastructure agent group?
● Yes. Using the Filter with a “Member of Group” fi
2. How could you identify agents where the plugins have not updated in the last 24 hours?
● Create a fi using the “Plugin update last updated on” fi
Scanner Groups
Part 1 – Create and Use a Scanner Group
Scanner groups can be used to combine scanners for load balancing scans, as well as assigning permissions to
scanners. In this section, create a scanner group and launch a scan using that group.
Part 1: Task 1 – Create a Scanner Group
Create a scanner group called Headquarters with a range of 10.0.0.0/24.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management.
3. Click the Menu in the upper left corner and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Scanner Groups .
6. Click +Add Scanner Group .
7. Type Headquarters in the Group Name fi
8. Type 10.0.0.0/24 in the Targets for Scan Routing fi
9. Click Can Use next to All Users , and select No Access .
10. Click the plus sign (+) next to Users & Groups . Search and select your username, and click Add .
11. Confirm that it says “Can use” next to your username.
12. Click Save .
Part 1: Task 2 – Add Scanners to the Headquarters Scanner Group
Add the two scanners with your name (other than the AWS scanner) to the Headquarters scanner group.
Note: This lab requires you to have completed Module 27 – Nessus Installation in order to complete this section.
Step-by-step Instructions:
1. Click the Menu and select Settings .
2. Click Sensors located in the Scanning section.
3. Click Scanner Groups .
4. Click Headquarters .
5. Click Assign Scanners .
6. Select the scanner named AWS-Student-Lab-Scanner_Scanner .
7. Click Assign .
Part 1: Task 3 – Scan Headquarters Using the Headquarters Scanner Group
Launch a credentialed scan of Headquarters using your new scanner group.
Step-by-step Instructions:
1. Click Quick Actions and select Create a VM Scan .
2. Click Basic Network Scan .
3. Type Headquarters scan using the scanner group in the Name fi
4. Select Headquarters from the Scanner drop-down.
5. Type 10.0.0.0/24 in the Targets fi
6. Click Credentials from the Settings menu.
7. Click plus sign (+) to the right of Add Credentials .
8. Open the Managed Credentials drop-down from the Select Credential Type panel that expanded on the
right.
9. Click HQ Windows Credentials .
10. Click HQ Linux Credentials} .
11. Click the X to close the window.
12. Click Save & Launch .
Part 1: Task 4 – Use the Auto-Select Option for Scans
Once a scanner group has been created, scanners can be automatically selected. Edit the scan named
“Headquarters scan using the scanner group” so that the scanner is automatically assigned.
Step-by-step Instructions:
1. Click the Menu button in the upper left corner, and select Scans .
2. Right-click Headquarters scan using the scanner group and select Edit.
3. Click Headquarters underneath Scanner and select Auto-Select .
4. Click Save .
Answer Key
Part 1: Task 1
1. How many scanners are associated with this scanner group?
● 0
2. Can you have two scanner groups with the same IP ranges?
● Yes
Part 1: Task 2
1. Are both scanners available in this group? How can you tell?
● Yes, because they both show as being online.
2. What are the IP addresses of the two scanners?
● 10.0.0.180 and 10.0.0.184
Part 1: Task 3
1. How can you tell that both scanners were used in this scan? (Hint: Look at plugin in ID 19506.)
● Filter on Plugin ID 19506 and “Plugin output contains Scanner IP : 10.0.0.180”. See which assets
are listed. Then, change the fi to “Plugin output contains Scanner IP : 10.0.0.184” and confirm
you have different assets.
2. How can you check to see if this scan ran faster than the previous scan?
● Click a scan, then click History to see scan time. You may compare the two.
Part 1: Task 4
1. When would there be problems using “Auto Select” for a scanner?
● When scanner groups have not been created for the range being scanned (i.e., the range being
scanned has not been entered into the “Targets for scan routing” fi
● When you have two network partitions that occupy the same IP address range.
2. Is it possible to have a scanner group with just one scanner in it? Why would you do this?
● Yes. You would do this so that you can use the Auto-Select option for scans. This also makes it
easier to maintain scans if you have to replace the scanner, since you only have to edit the
scanner group, and not each individual scan.
Networks
Part 1 – Networks
In this section, use networks when there are two network partitions using the same IP address range. Networks
allow you to differentiate the two networks for asset identification and scanning purposes.
NOTE: All of the tasks in Part 2 assume you are in a continuous session. Stay logged in after completing Part 1.
Part 1: Task 1 – Create a Headquarters Network
A recent acquisition of another company has resulted in there being two network partitions with the IP range
10.0.0.0/24. Create a network for Headquarters.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click Vulnerability Management .
3. Click the Menu and select Settings .
4. Click Sensors located in the Scanning section.
5. Click Networks .
6. Click Add Network .
7. Type HQ Network in the Name fi
8. Click Create .
9. Click Save .
Part 1: Task 2 – Add Scanners and Move Assets
Once a network has been created, add scanners. Moving assets to the network is optional .
Step-by-step Instructions:
1. Click Move Assets in the Settings menu.
2. Select Default from the Network drop-down.
3. Type 10.0.0.0/24 in the Default fi
4. Click Search .
Part 2: Task 3 – Add HQ Assets to Network
Add the HQ assets to the network.
Step-by-step Instructions:
1. Select the check box to the left of assets.
2. Click Select all #### Assets .
3. Click the word Move (to the right of Select all <number> assets ).
Answer Key
Part1: Task 1
1. Can you assign the single scanner AWS-Student-Lab-Scanner_Scanner to the network? Why?
● No. Because the scanner is in a scanner group, you can only assign the scanner group.
2. Is it acceptable to assign the scanner group to this network?
● Yes. Both scanners can reach this range, so using both of them will be alright.
Part 1: Task 2
1. How can you fi the assets that have been scanned with Nessus (and therefore are part of HQ)?
● Click the Source column until the assets that have Nessus scan results are at the top.
Part 1: Task 3
1. Go to Assets, under Explore. Is there a way to view data on just the HQ Network?
● Yes. Search for and use the Network fi
2. From the Network window, there is no way to remove an asset from the network. Is there another way to
remove an asset from a network?
● Yes. From the Asset window you can click the Move icon (→) to move an asset to another
network, or to the default network.
Permissions & Access Control
Lab Exercise 36: Setting Up Permissions with Tags
Part 1 – Create a Tag for All Windows Assets at HQ
In this section, create a tag based on rules.
Part 1: Task 1 – Create a Tag
Create a tag based on the operating system, and a range of IPv4 addresses.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu in the upper left corner and select Settings .
3. Click Tagging .
4. Click + Create Tag .
5. Type HQ Assets in the Select or Create Category fi
6. Click Create “HQ Assets” below.
7. Type Windows in the Create Value fi
8. Enable the Rules slider.
9. Click Select Filters .
10. Search for and select IPv4 Address .
11. Search for and select Operating System .
12. Click the X to close the Select Filters pop-out.
13. Click IPv4 Address: is equal to “” , and type 10.0.0.0/24 in the fi below is equal to .
14. Click Save .
15. Click Operating System: is equal to “” , and type *indows* in the fi below is equal to .
16. Click Save .
17. Wait a few minutes for the tag to take effect before answering the challenge questions. You may
proceed to the next task and come back to them.
Part 2 – Edit Permissions
In this section, update your default permissions, as well as the permissions for your newly created tag.
Part 2: Task 1 – Edit Default Permissions
Edit the “Access all Assets” permission to restrict access.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu icon in the upper left corner and select Settings .
3. Click Access Control .
4. Click Permissions .
5. Click Access All Assets .
6. Click the X under Groups to remove the All Users group.
7. Locate Users , and then select your username.
8. Click Save .
Part 2: Task 2 – Edit the Permissions Related to the New Tag
A new permission exists in relation to the tag created in the fi task. Edit this permission so that assigned
users or user groups can use the tag for analysis and scanning.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu icon in the upper left corner and select Settings .
3. Click Access Control .
4. Click Permissions .
5. Click the Permission tag ‘HQ Assets:WIndows’ owner permissions .
6. Click in the Permission Name , and edit it to HQ Windows Assets .
7. Click the X in the Permissions fi to remove the Can Edit permission.
8. Click the drop-down in the Permissions fi and enable both Can Scan and Can View .
9. Click Save .
Answer Key
Part 1: Task 1
1. How many assets were tagged?
● The number will vary depending upon the lab environment, but there should be at least 5 or
more assets.
2. How would you create a tag that fi on DNS names?
● Enable Rules , and select the DNS (FQDN) fi You can also set this same fi in
Explore>Assets , to immediately see if you have the results you want. Then, click the tag icon
from the Assets page to create the tag there, based on that fi Just be aware that there are
other default fi on that page that you may wish to remove fi
Part 2: Task 1
1. How else could you restrict access to assets for all users?
● You can simply delete the Access all Assets permission, or create a specific user group and
assign that group instead. Remember that administrator users will still have access to
everything regardless of permissions though. Role always supersedes permissions.
Part 2:Task 2
1. Who can currently access and scan the tagged HQ Windows assets?
● All Administrator users, by default. No other users can as no other users or user groups have yet
been assigned this permission.
3. Can a permission have more than one tag?
● Yes, however, the IPv4 address or IPv6 address rules must be different in the different tags.
Lab Exercise 37: Users, Roles, and User Groups
Part 1 – Create a Group for IT Administrators in HQ
In this section, you have an HQ IT team. Create an access group and a user group for the team.
Part 1: Task 1 – Create a User Group
Create a user group for Headquarters.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu in the upper left corner and select Settings .
3. Click Access Control .
4. Click Groups .
5. Click + Create Group .
6. Type HQ Security Group in the Name fi
7. Click Next .
8. Click Save .
Part 1: Task 2 – Create Permissions and Assign to User Group
Now that access controls are set, assign the permissions.
Step-by-step Instructions:
1. Click the Menu and select Settings .
2. Click Access Control .
3. Click Permissions .
4. Click Create Permission .
5. Select HQ-Security from the Permission Name fi
6. Click underneath Groups and select the user group you created in the previous task: HQ Security Group .
7. Select Can View from the Permission drop-down.
8. Select Can Scan from the Permission drop-down.
9. Repeat Step 8 for Can Use.
a. The Permissions fi should now display: Can View, Can Scan, Can Use
10. Select Regions:HQ from the Objects drop-down.
11. Click Save .
Part 1: Task 3 – Create a user and assign to the User Group
Create a new user, and assign to the user group.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the initials in the top right corner of the screen, and select My Profile .
3. Locate the email fi and copy the domain (the part after the @) to your clipboard.
4. Click Cancel .
5. Click the Menu in the upper left corner and select Settings .
12. Click Access Control .
13. Click Users .
14. Click Create User .
15. Type Jake Doe in the Full Name fi
16. Type jdoe@{domain} in the Username fi
a. Note: The domain is pasted from the domain you copied to your clipboard in Step 3 above.
17. Type Training@12345!a in the Password fi
18. Type the same password from Step 17 above into the Verify Password fi
19. Select the Scan Manager role.
20. Click Next .
21. Click the User Groups drop-down menu, and select HQ Security Group .
22. Click Next .
23. Click Save .
Answer Key
Part 1: Task 1
1. Have any members been added to this group?
● No, not yet.
Part 1: Task 2
1. Are users in the assigned user group able to edit the created permission?
● It depends on the user’s role. Administrator users can edit objects, regardless of their assigned
permissions. All other users would not be able to edit the permission, however, unless “Can Edit”
permission is explicitly assigned.
Part 1:Task 3
1. Why didn’t we assign any permissions in the Create User form?
● User permissions were not necessary, since the permissions were assigned at the user group
level instead.
2. Can a user be in more than one group?
● Yes. It’s important to track what groups you assign a user to, in order to ensure that the user will
have the correct permissions.
Lab Exercise 38: Object User Permissions
Part 1 – Assign Execute Permissions for a Scan
In this section, there are users in the HQ Security Group that need access to a scan that you have set up.
Part 1: Task 1 – Edit an Existing Scan, and Assign User Permissions to a User Group
Assign scan permissions to a user group so that they can control a scan.
Step-by-step Instructions:
1. Ensure you are logged into Tenable Vulnerability Management via cloud.tenable.com with the
credentials provided.
2. Click the Menu in the upper left corner and select Scans .
3. Click the Actions menu (⠇) to the right of Credentialed Scan of HQ , and select Edit .
4. Locate the Basic tab, and scroll down to the User Permissions section. click the plus (+) sign next to
User Permissions .
5. Search for and select HQ Security Group .
6. Click the permission drop-down next to HQ Security Group , and select Can Execute . (This should be the
default.)
7. Click Add then Save.
Answer Key
Part 1: Task 1
1. What users have access to manage this scan?
● All Administrator users, and all users that belong to the HQ Security Group .
2. How can you verify that you have set permissions correctly?
● Use the User Assist function for one of the users within the user group, to see what that user
can see and do.
3. What permission would you select if you wanted the users in the group to be able to update any settings
in the scan?
● Can Edit