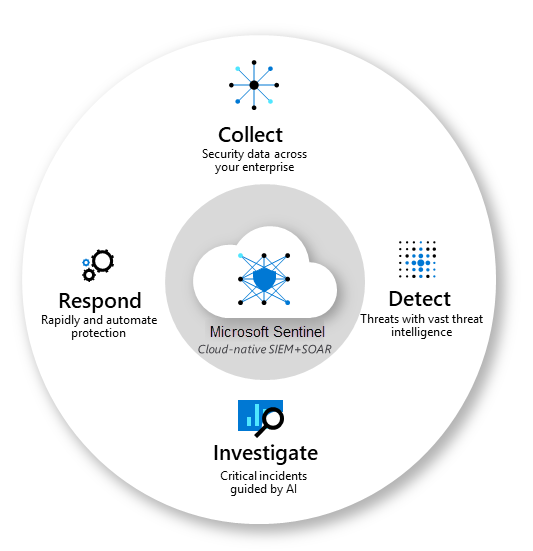
Microsoft Sentinel is a scalable, cloud-native solution that provides:
- Security information and event management (SIEM)
- Security orchestration, automation, and response (SOAR)
Microsoft Sentinel delivers intelligent security analytics and threat intelligence across the enterprise. With Microsoft Sentinel, you get a single solution for attack detection, threat visibility, proactive hunting, and threat response.
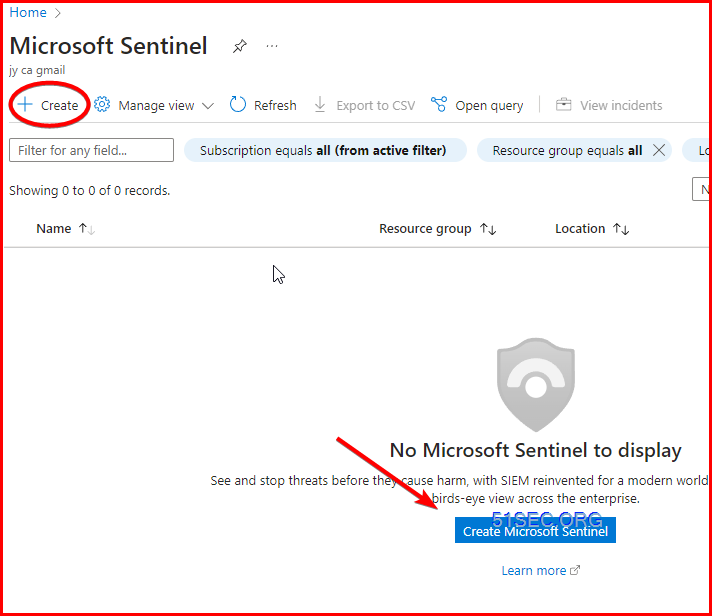
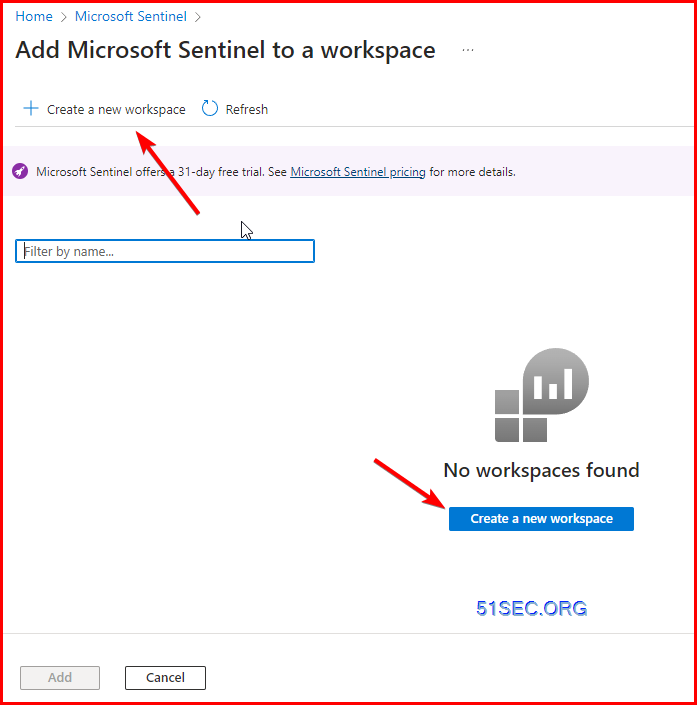
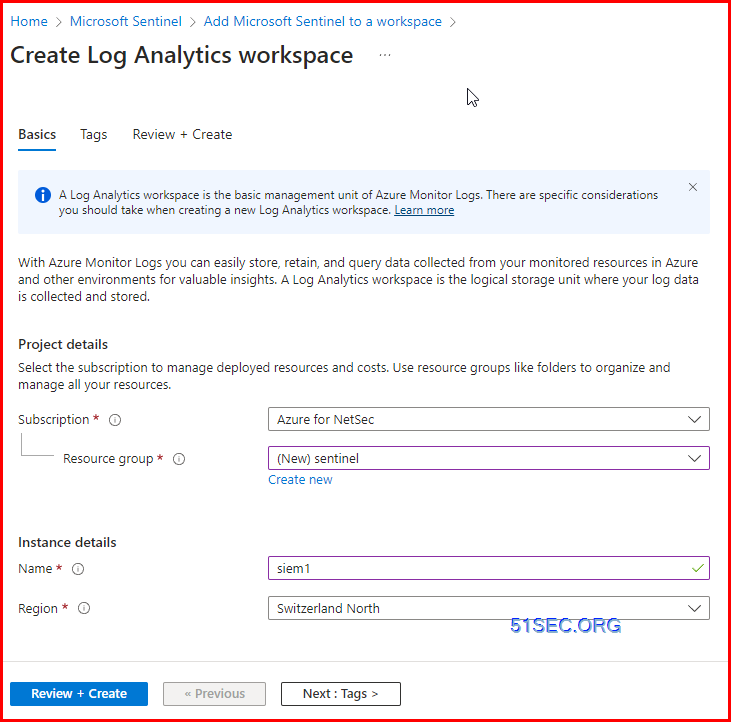
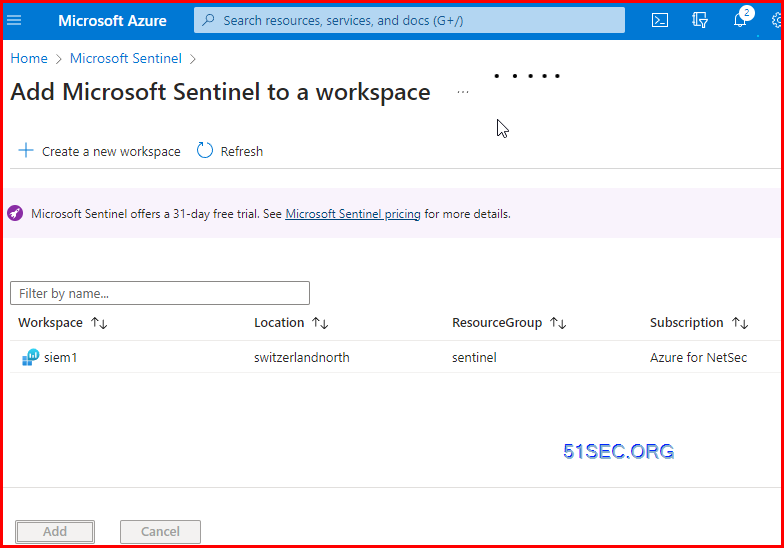
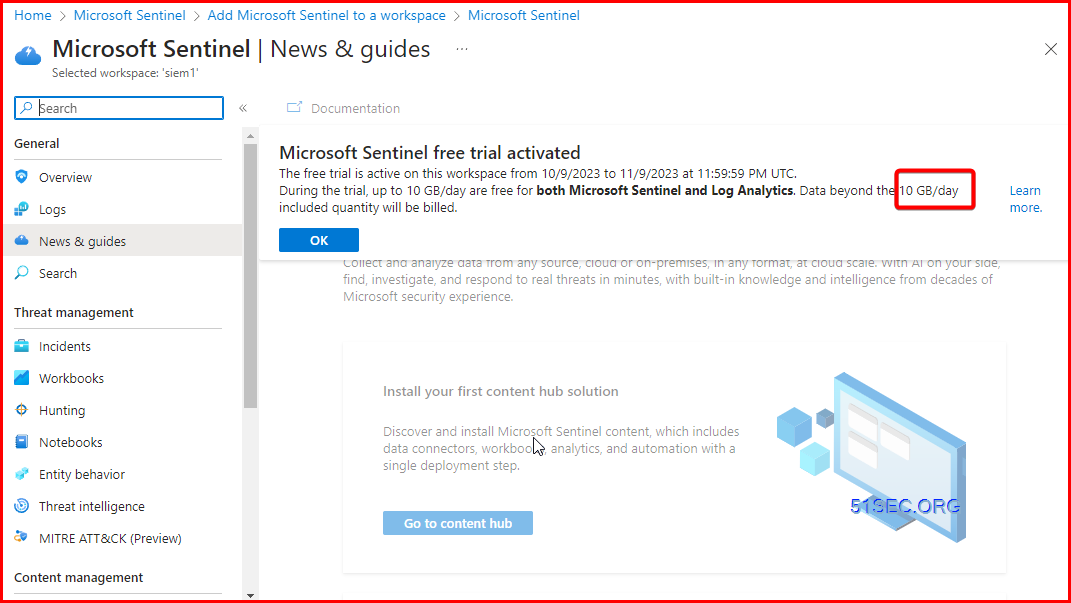
Create Microsoft Sentinel and Log Analytics Workspace
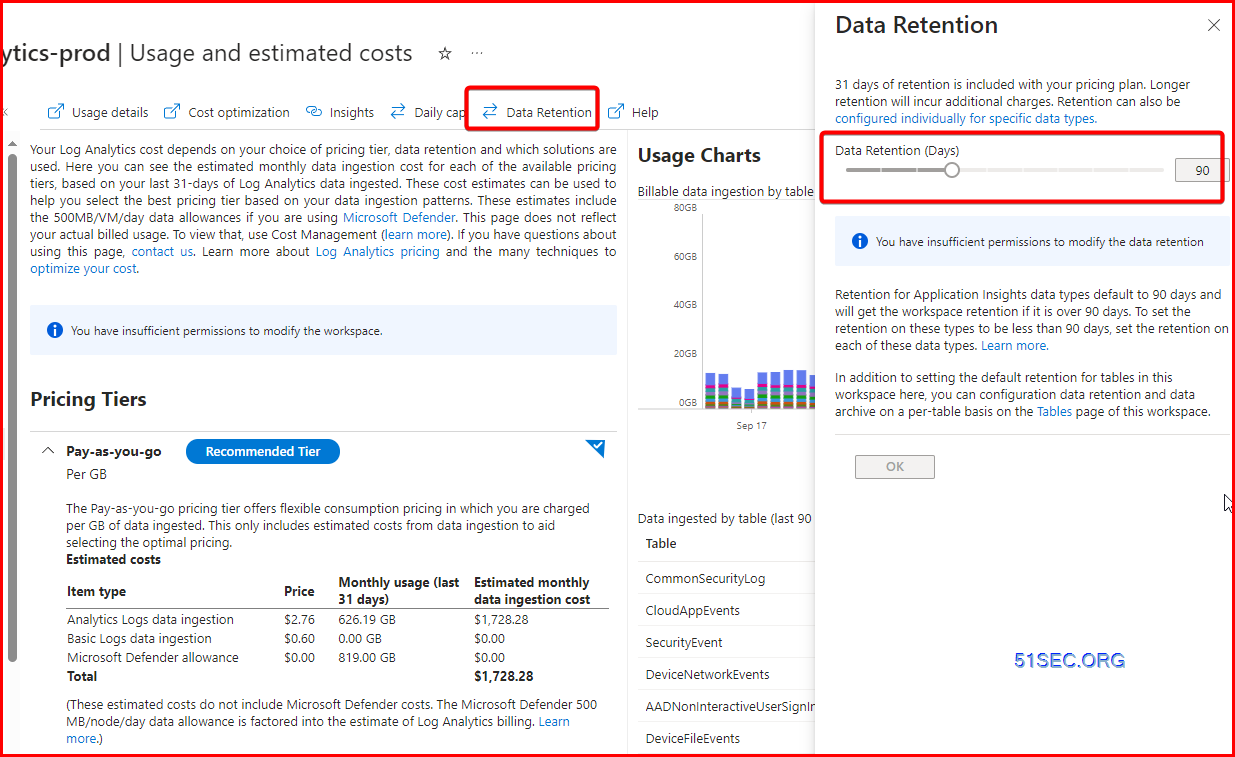
A single Log Analytics workspace might be sufficient for many environments that use Azure Monitor and Microsoft Sentinel. But many organizations will create multiple workspaces to optimize costs and better meet different business requirements.
Dedicated workspaces Creating dedicated workspaces for Azure Monitor and Microsoft Sentinel will allow you to segregate ownership of data between operational and security teams. This approach may also help to optimize costs since when Microsoft Sentinel is enabled in a workspace, all data in that workspace is subject to Microsoft Sentinel pricing even if it’s operational data collected by Azure Monitor.
A workspace with Microsoft Sentinel gets three months of free data retention instead of 31 days. This scenario typically results in higher costs for operational data in a workspace without Microsoft Sentinel.
=====================================
From: https://learn.microsoft.com/en-us/azure/azure-monitor/logs/data-retention-archive?tabs=portal-1%2Cportal-2
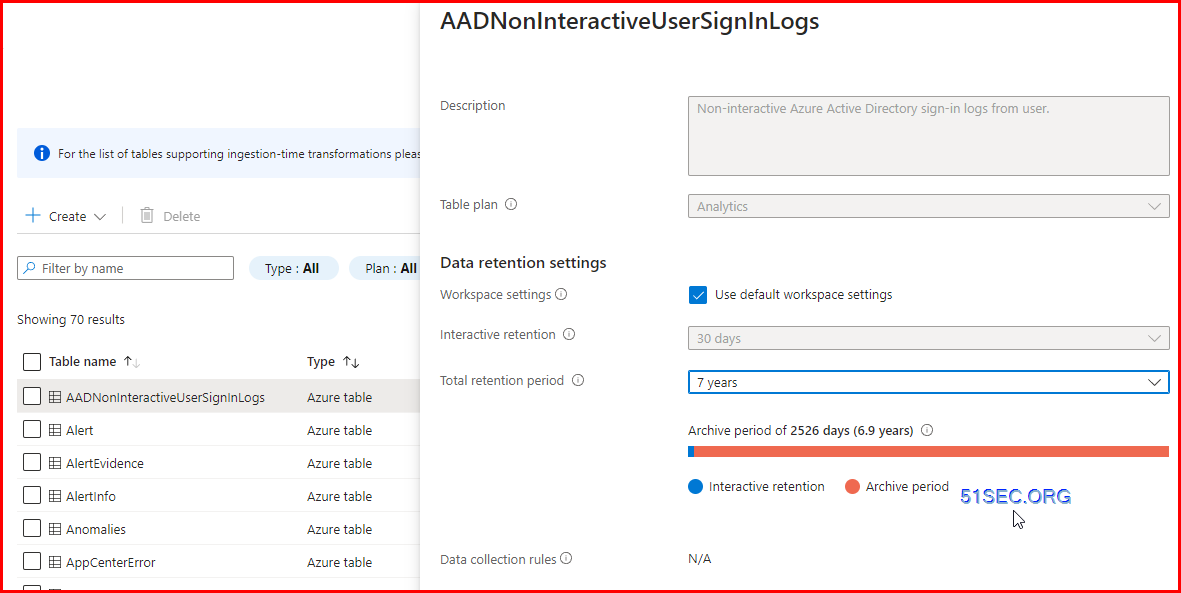
By default, all tables in your workspace inherit the workspace’s interactive retention setting and have no archive. You can modify the retention and archive settings of individual tables, except for workspaces in the legacy Free Trial pricing tier.
The Analytics log data plan includes 30 days of interactive retention. You can increase the interactive retention period to up to 730 days at an additional cost. If needed, you can reduce the interactive retention period to as little as four days using the API or CLI. However, since 30 days are included in the ingestion price, lowering the retention period below 30 days doesn’t reduce costs. You can set the archive period to a total retention time of up to 2,556 days (seven years).
Combined workspace Combining your data from Azure Monitor and Microsoft Sentinel in the same workspace gives you better visibility across all of your data allowing you to easily combine both in queries and workbooks. If access to the security data should be limited to a particular team, you can use table level RBAC to block particular users from tables with security data or limit users to accessing the workspace using resource-context.
This configuration may result in cost savings if it helps you reach a commitment tier, which provides a discount to your ingestion charges. For example, consider an organization that has operational data and security data each ingesting about 50 GB per day. Combining the data in the same workspace would allow a commitment tier at 100 GB per day. That scenario would provide a 15% discount for Azure Monitor and a 50% discount for Microsoft Sentinel.
If you create separate workspaces for other criteria, you’ll usually create more workspace pairs. For example, if you have two Azure tenants, you might create four workspaces with an operational and security workspace in each tenant.
- If you use both Azure Monitor and Microsoft Sentinel: Consider separating each in a dedicated workspace if required by your security team or if it results in a cost savings. Consider combining the two for better visibility of your combined monitoring data or if it helps you reach a commitment tier.
- If you use both Microsoft Sentinel and Microsoft Defender for Cloud: Consider using the same workspace for both solutions to keep security data in one place.
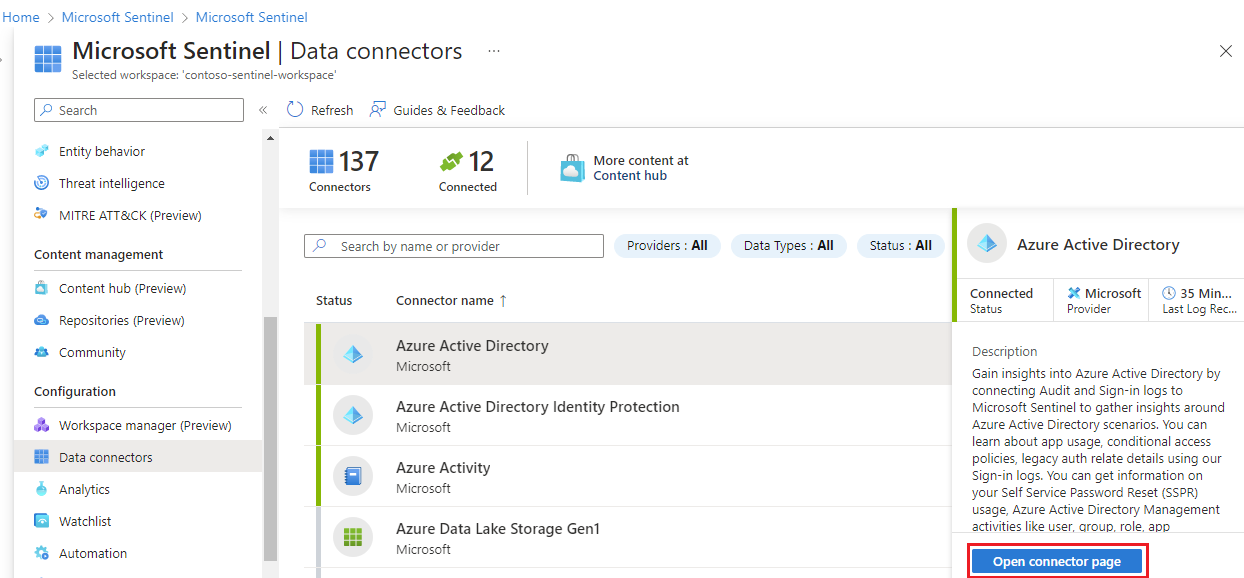
Collect data by using data connectors
To on-board Microsoft Sentinel, you first need to connect to your data sources.
Microsoft Sentinel comes with many connectors for Microsoft solutions that are available out of the box and provide real-time integration. Some of these connectors include:
- Microsoft sources like Microsoft 365 Defender, Microsoft Defender for Cloud, Office 365, Microsoft Defender for IoT, and more.
- Azure service sources like Azure Active Directory, Azure Activity, Azure Storage, Azure Key Vault, Azure Kubernetes service, and more.
Microsoft Sentinel has built-in connectors to the broader security and applications ecosystems for non-Microsoft solutions. You can also use common event format, Syslog, or REST-API to connect your data sources with Microsoft Sentinel.
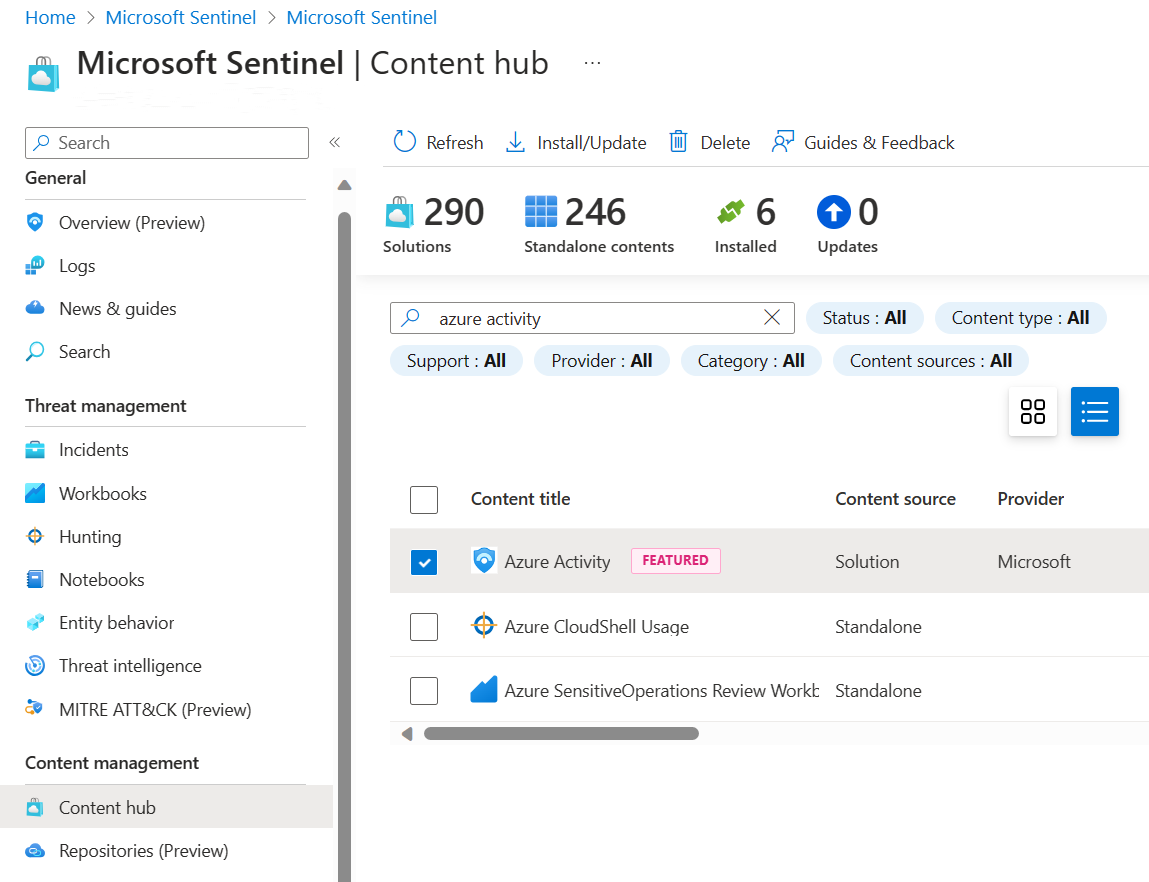
1 Install a solution from the content hub
Azure Activity Log: https://portal.azure.com/#view/Microsoft_Azure_Monitoring/AzureMonitoringBrowseBlade/~/activityLog
The content hub in Microsoft Sentinel is the centralized location to discover and manage out-of-the-box content including data connectors. For this quickstart, install the solution for Azure Activity.
-
In Microsoft Sentinel, select Content hub.
-
Find and select the Azure Activity solution.
2 Set up the data connector
Microsoft Sentinel ingests data from services and apps by connecting to the service and forwarding the events and logs to Microsoft Sentinel. For this quickstart, install the data connector to forward data for Azure Activity to Microsoft Sentinel.
-
In Microsoft Sentinel, select Data connectors.
-
Search for and select the Azure Activity data connector.
-
In the details pane for the connector, select Open connector page.
-
Review the instructions to configure the connector.
-
Select Launch Azure Policy Assignment Wizard.
-
On the Basics tab, set the Scope to the subscription and resource group that has activity to send to Microsoft Sentinel. For example, select the subscription that contains your Microsoft Sentinel instance.
-
Select the Parameters tab.
-
Set the Primary Log Analytics workspace. This should be the workspace where Microsoft Sentinel is installed.
-
Select Review + create and Create.
3 Generate activity data
Let’s generate some activity data by enabling a rule that was included in the Azure Activity solution for Microsoft Sentinel. This step also shows you how to manage content in the content hub.
-
In Microsoft Sentinel, select Content hub.
-
Find and select the Azure Activity solution.
-
From the right-hand side pane, select Manage.
-
Find and select the rule template Suspicious Resource deployment.
-
Select Configuration.
-
Select the rule and Create rule.
-
On the General tab, change the Status to enabled. Leave the rest of the default values.
-
Accept the defaults on the other tabs.
-
On the Review and create tab, select Create.
4 View data ingested into Microsoft Sentinel
Now that you’ve enabled the Azure Activity data connector and generated some activity data let’s view the activity data added to the workspace.
-
In Microsoft Sentinel, select Data connectors.
-
Search for and select the Azure Activity data connector.
-
In the details pane for the connector, select Open connector page.
-
Review the Status of the data connector. It should be Connected.
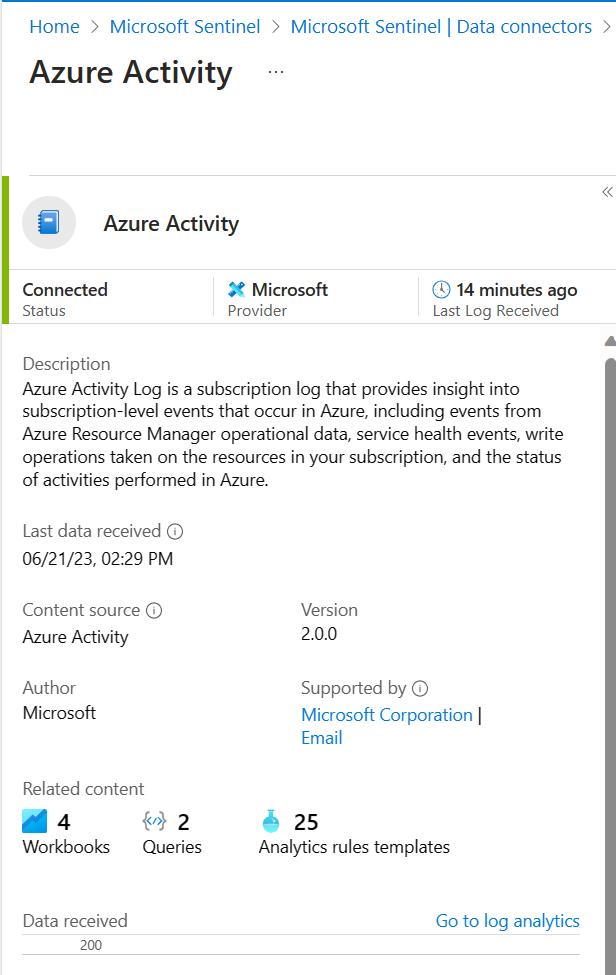
-
In the left-hand side pane above the chart, select Go to log analytics.
-
On the top of the pane, next to the New query 1 tab, select the + to add a new query tab.
-
In the query pane, run the following query to view the activity date ingested into the workspace.
KustoAzureActivity
Create interactive reports by using workbooks
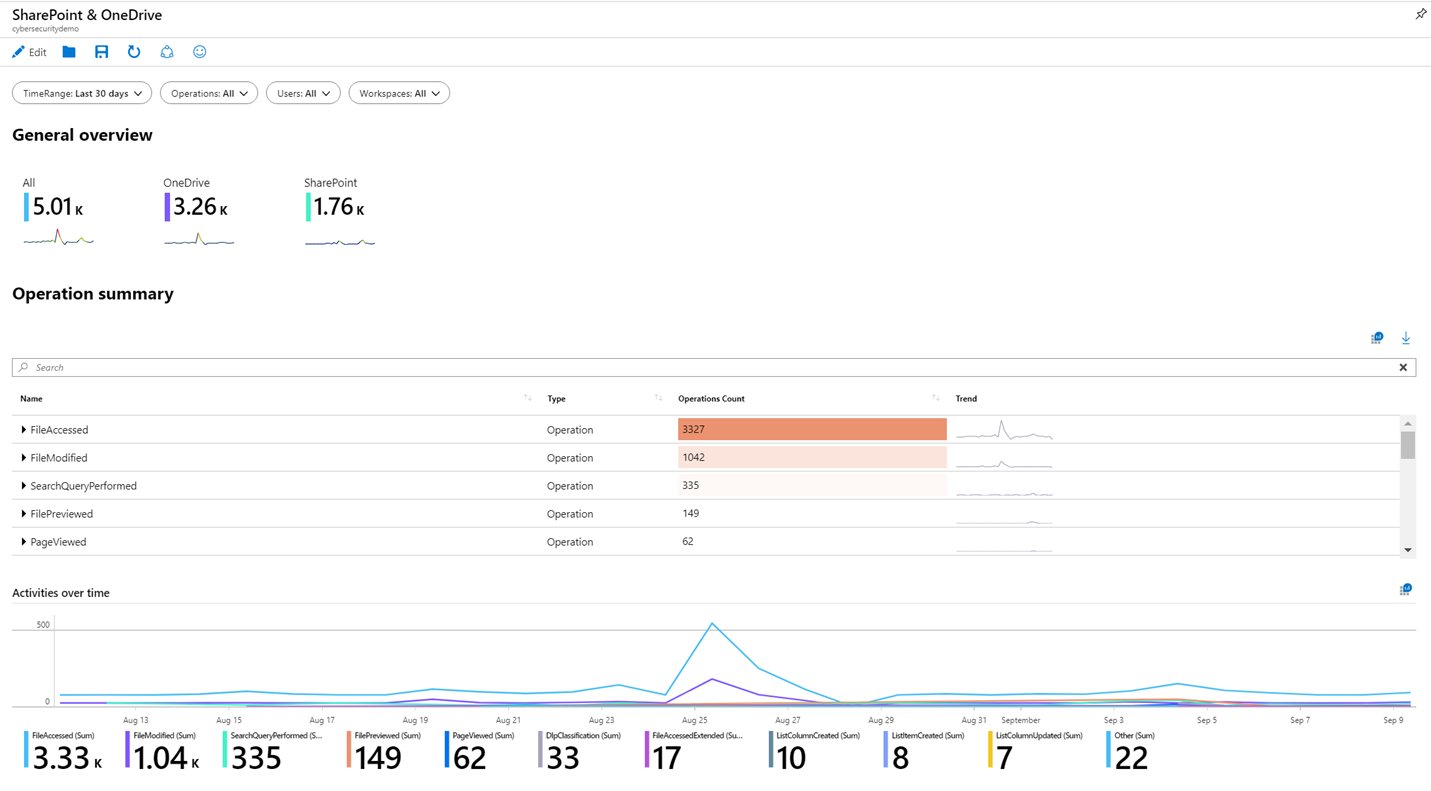
After you onboard to Microsoft Sentinel, monitor your data by using the integration with Azure Monitor workbooks.
Workbooks display differently in Microsoft Sentinel than in Azure Monitor. But it may be useful for you to see how to create a workbook in Azure Monitor. Microsoft Sentinel allows you to create custom workbooks across your data. Microsoft Sentinel also comes with built-in workbook templates to allow you to quickly gain insights across your data as soon as you connect a data source.
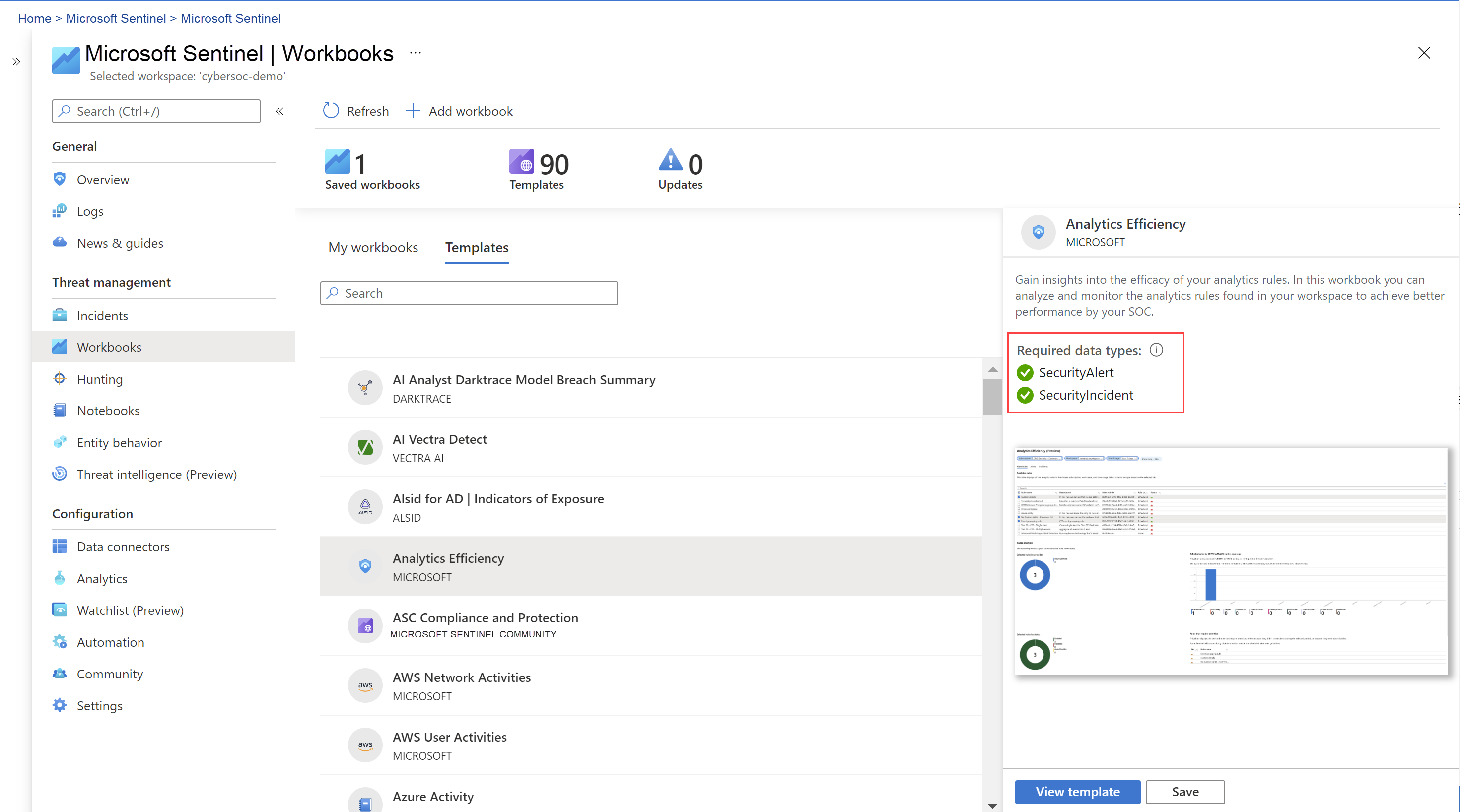
Workbooks are intended for SOC engineers and analysts of all tiers to visualize data.
Workbooks are best used for high-level views of Microsoft Sentinel data, and don’t require coding knowledge. But you can’t integrate workbooks with external data.
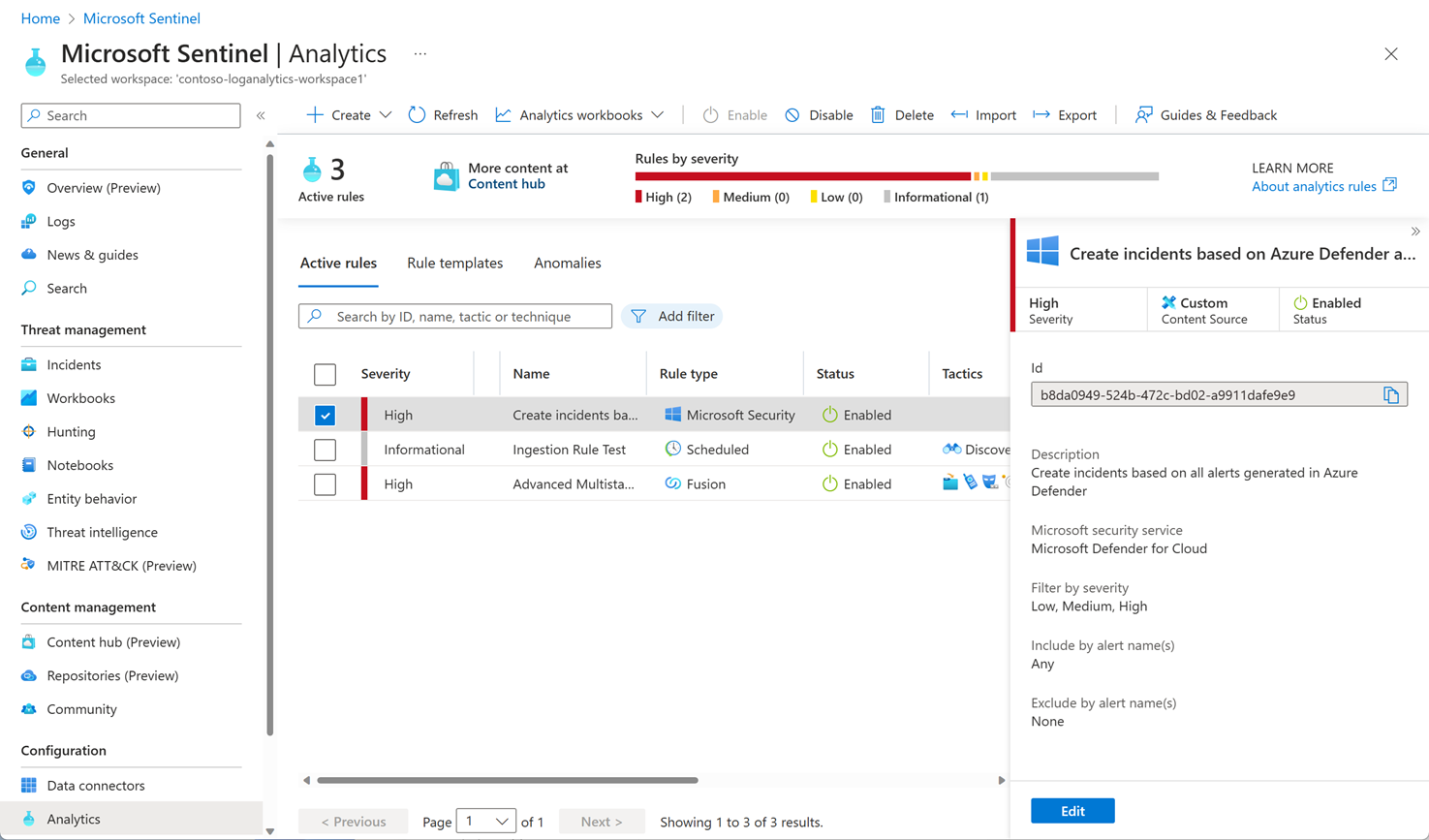
Correlate alerts into incidents by using analytics rules
To help you reduce noise and minimize the number of alerts you have to review and investigate, Microsoft Sentinel uses analytics to correlate alerts into incidents. Incidents are groups of related alerts that together indicate an actionable possible-threat that you can investigate and resolve. Use the built-in correlation rules as-is, or use them as a starting point to build your own. Microsoft Sentinel also provides machine learning rules to map your network behavior and then look for anomalies across your resources. These analytics connect the dots, by combining low fidelity alerts about different entities into potential high-fidelity security incidents.
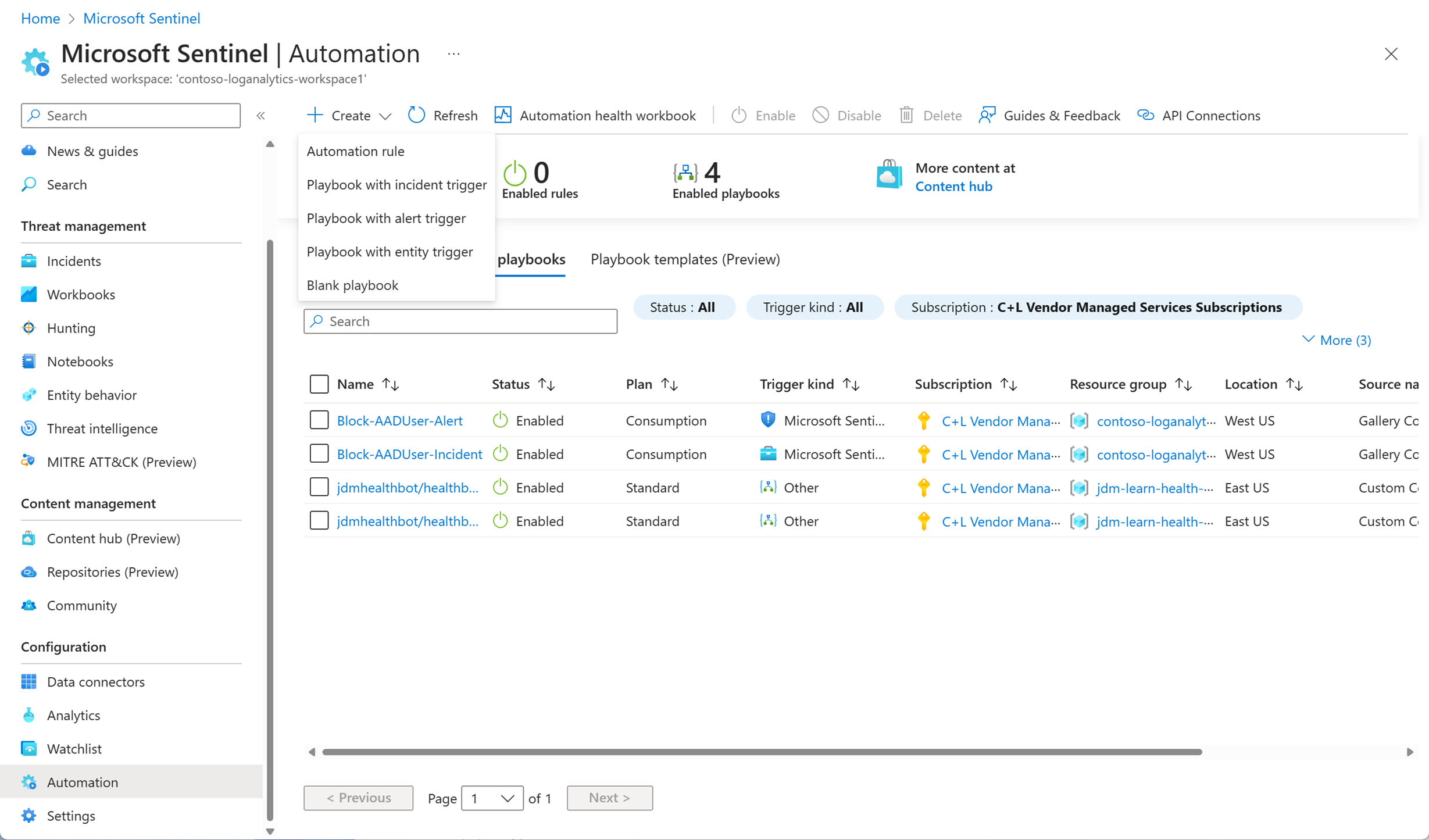
Automate and orchestrate common tasks by using playbooks
Automate your common tasks and simplify security orchestration with playbooks that integrate with Azure services and your existing tools.
Microsoft Sentinel’s automation and orchestration solution provides a highly extensible architecture that enables scalable automation as new technologies and threats emerge. To build playbooks with Azure Logic Apps, you can choose from a constantly expanding gallery with many hundreds of connectors for various services and systems. These connectors allow you to apply any custom logic in your workflow, for example:
- ServiceNow
- Jira
- Zendesk
- HTTP requests
- Microsoft Teams
- Slack
- Azure Active Directory
- Microsoft Defender for Endpoint
- Microsoft Defender for Cloud Apps
For example, if you use the ServiceNow ticketing system, use Azure Logic Apps to automate your workflows and open a ticket in ServiceNow each time a particular alert or incident is generated.
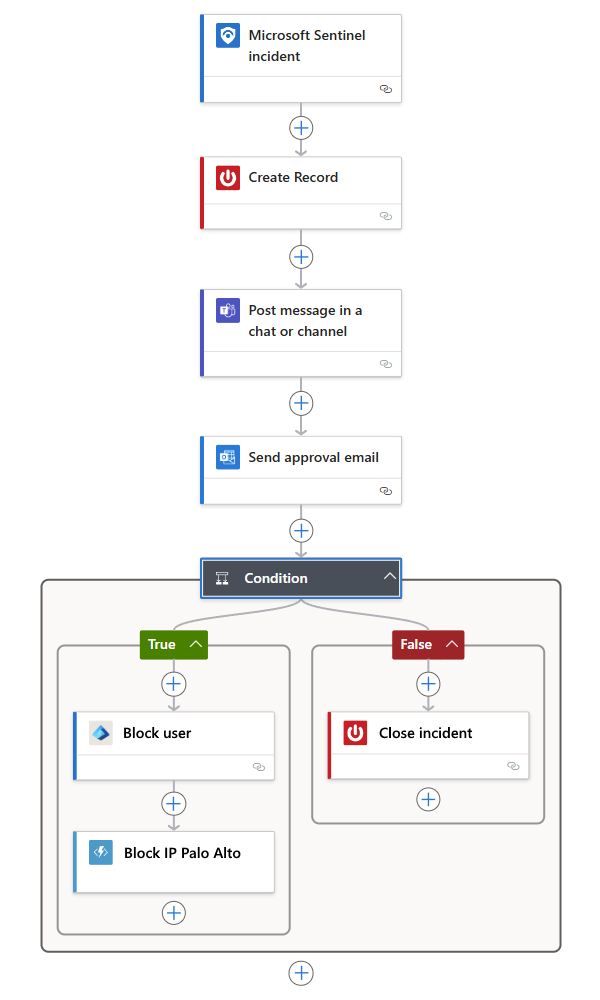
Playbooks are intended for SOC engineers and analysts of all tiers, to automate and simplify tasks, including data ingestion, enrichment, investigation, and remediation.
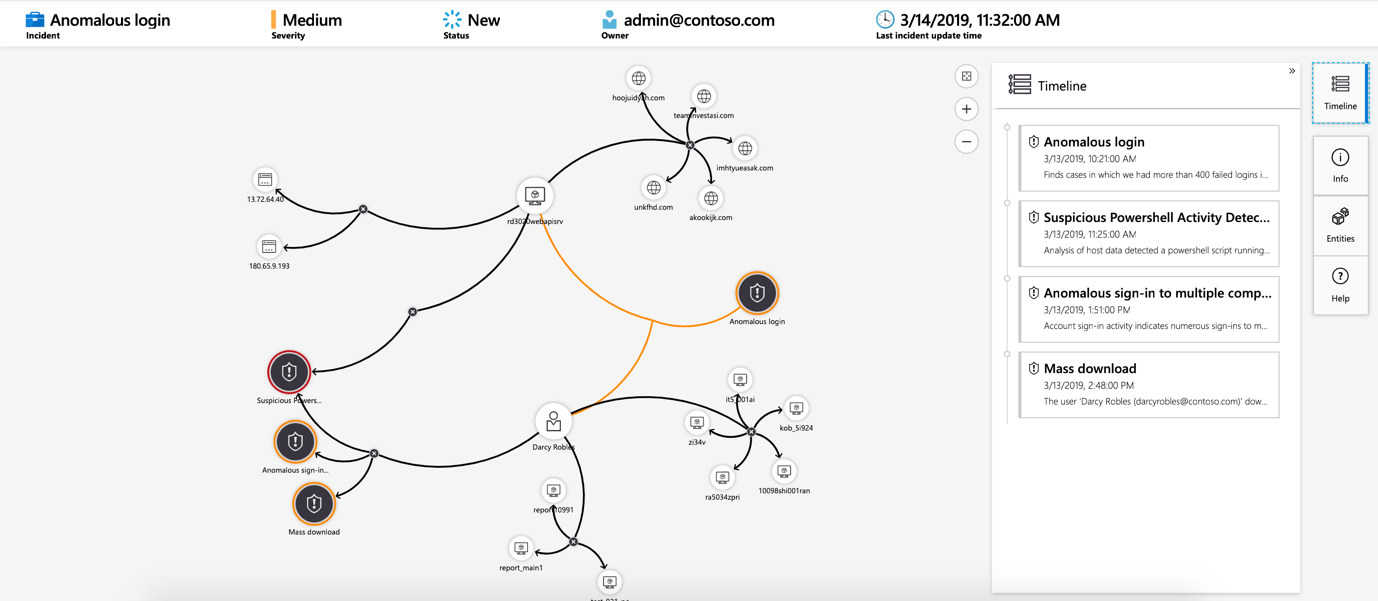
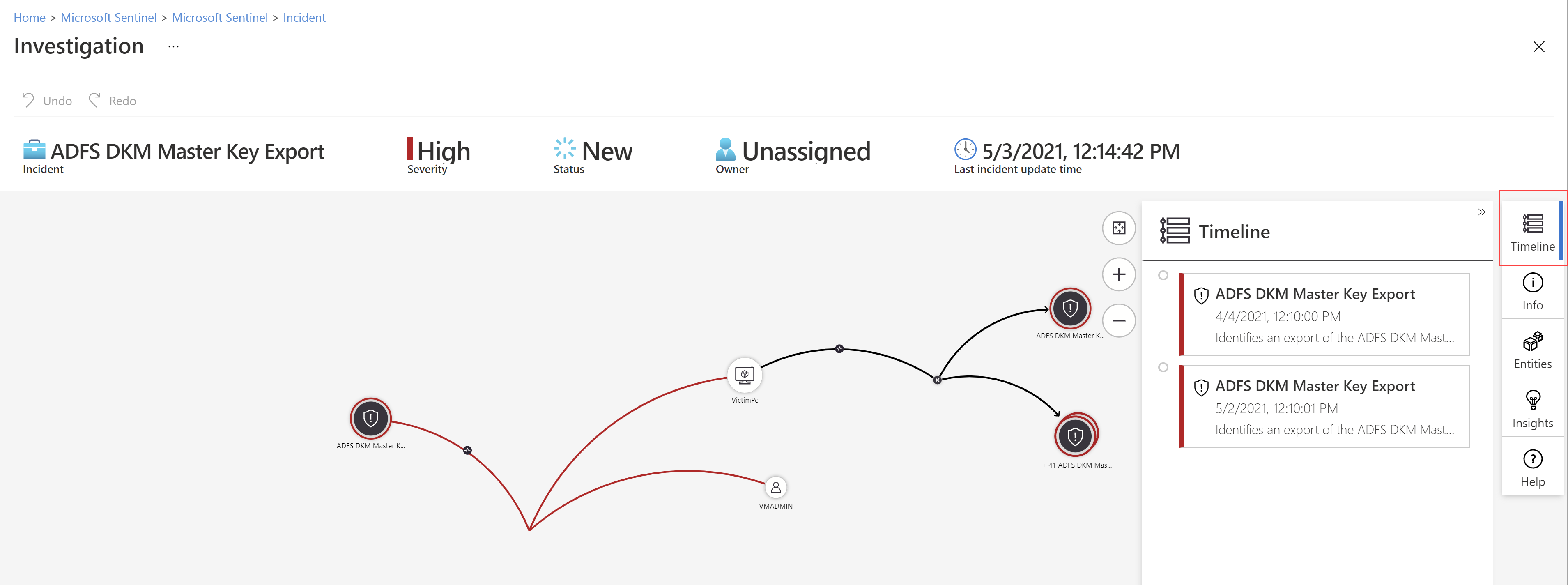
Investigate the scope and root cause of security threats
Microsoft Sentinel deep investigation tools help you to understand the scope and find the root cause of a potential security threat. You can choose an entity on the interactive graph to ask interesting questions for a specific entity, and drill down into that entity and its connections to get to the root cause of the threat.
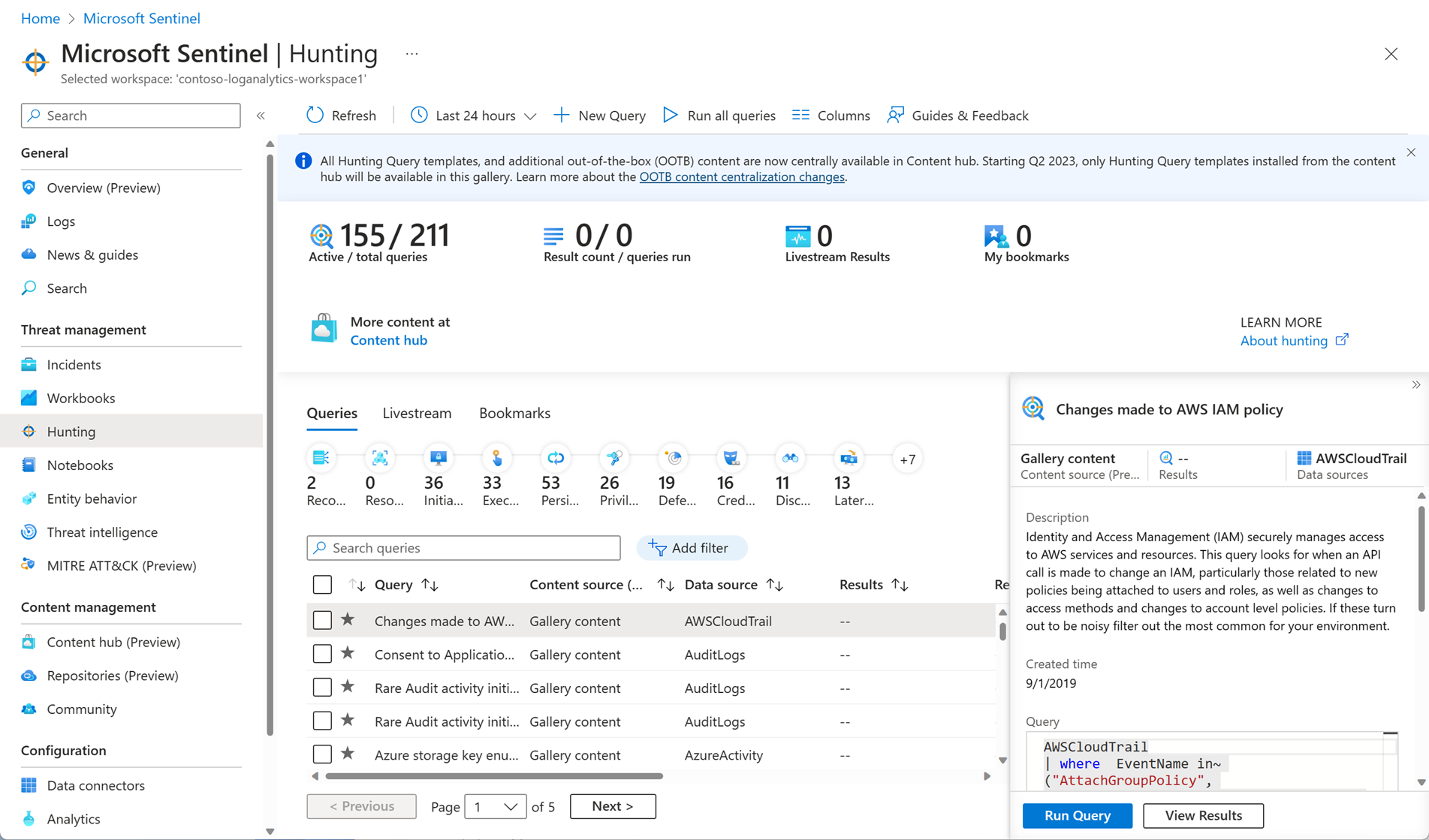
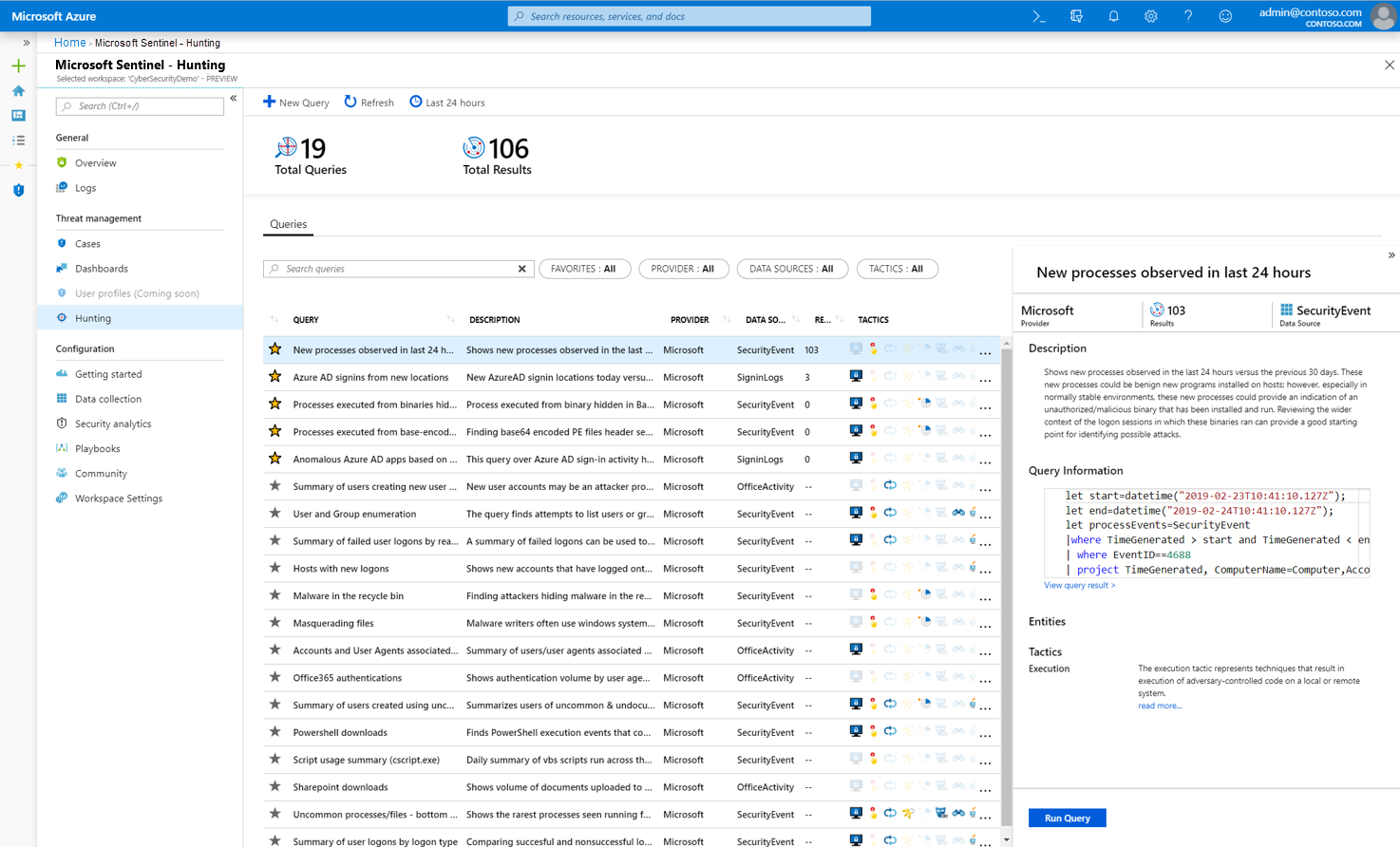
Hunt for security threats by using built-in queries
Use Microsoft Sentinel’s powerful hunting search-and-query tools, based on the MITRE framework, which enable you to proactively hunt for security threats across your organization’s data sources, before an alert is triggered. Create custom detection rules based on your hunting query. Then, surface those insights as alerts to your security incident responders.
While hunting, create bookmarks to return to interesting events later. Use a bookmark to share an event with others. Or, group events with other correlating events to create a compelling incident for investigation.
Enhance your threat hunting with notebooks
Microsoft Sentinel supports Jupyter notebooks in Azure Machine Learning workspaces, including full libraries for machine learning, visualization, and data analysis.
Use notebooks in Microsoft Sentinel to extend the scope of what you can do with Microsoft Sentinel data. For example:
- Perform analytics that aren’t built in to Microsoft Sentinel, such as some Python machine learning features.
- Create data visualizations that aren’t built in to Microsoft Sentinel, such as custom timelines and process trees.
- Integrate data sources outside of Microsoft Sentinel, such as an on-premises data set.
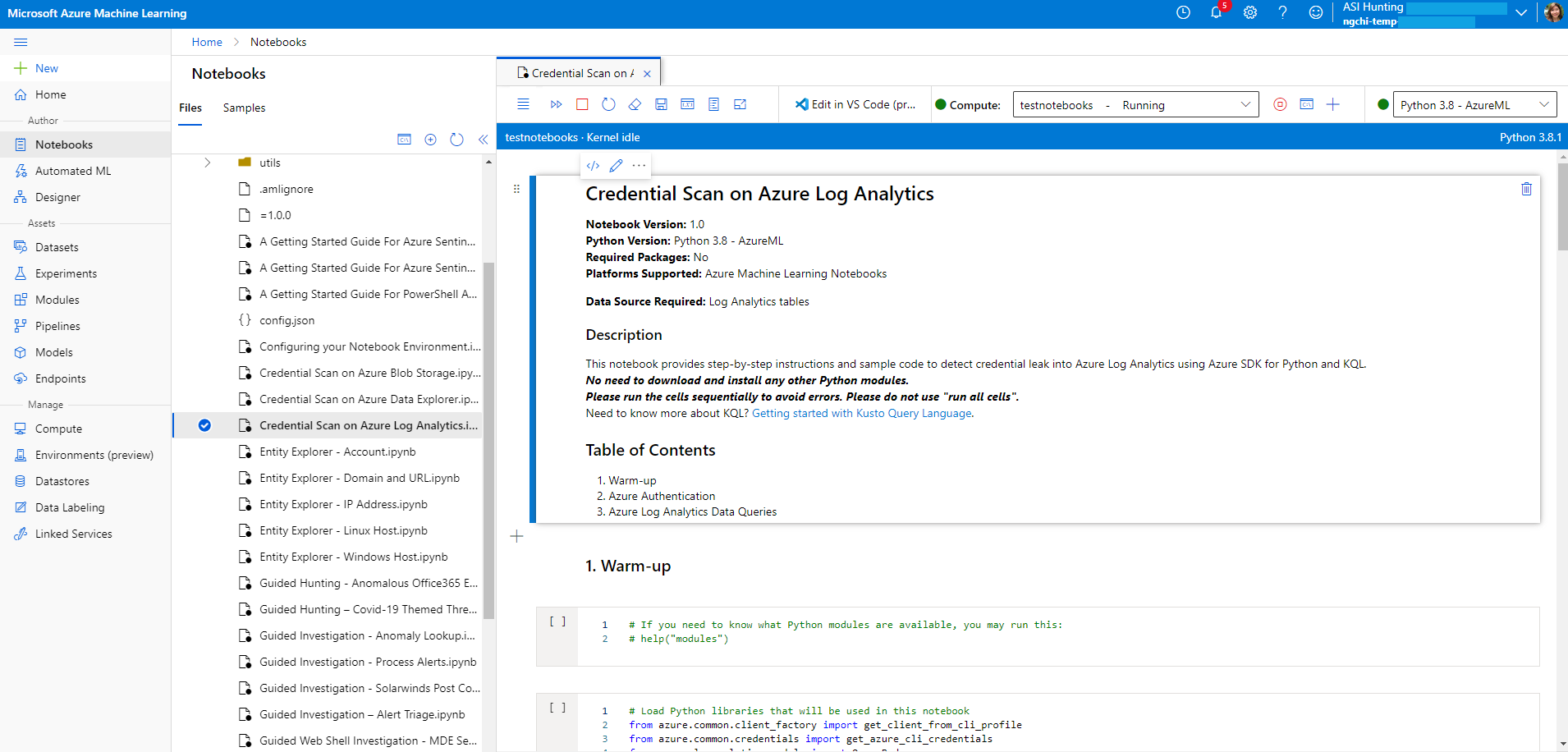
Notebooks are intended for threat hunters or Tier 2-3 analysts, incident investigators, data scientists, and security researchers. They require a higher learning curve and coding knowledge. They have limited automation support.
Notebooks in Microsoft Sentinel provide:
- Queries to both Microsoft Sentinel and external data
- Features for data enrichment, investigation, visualization, hunting, machine learning, and big data analytics
Notebooks are best for:
- More complex chains of repeatable tasks
- Ad-hoc procedural controls
- Machine learning and custom analysis
Notebooks support rich Python libraries for manipulating and visualizing data. They’re useful to document and share analysis evidence.
Workbooks
You can use workbooks to visualize your data within Microsoft Sentinel. Think of workbooks as dashboards. Each component in the dashboard is built by using an underlying KQL query of your data. You can use the built-in workbooks within Microsoft Sentinel and edit them to meet your own needs, or create your own workbooks from scratch. If you’ve used Azure Monitor workbooks, this feature will be familiar to you, because it’s Sentinel’s implementation of Monitor workbooks.
Analytics
You can enable built-in analytics alerts within your Sentinel workspace. There are various types of alerts, some of which you can edit to your own needs. Other alerts are built on machine-learning models that are proprietary to Microsoft. You can also create custom, scheduled alerts from scratch.
Threat Hunting
We won’t dive deeply into threat hunting in this module. However, if SOC analysts need to hunt for suspicious activity, there are some built-in hunting queries that they can use. Analysts can also create their own queries. Sentinel also integrates with Azure Notebooks. It provides example notebooks for advanced hunters who want to use the full power of a programming language to hunt through their data.
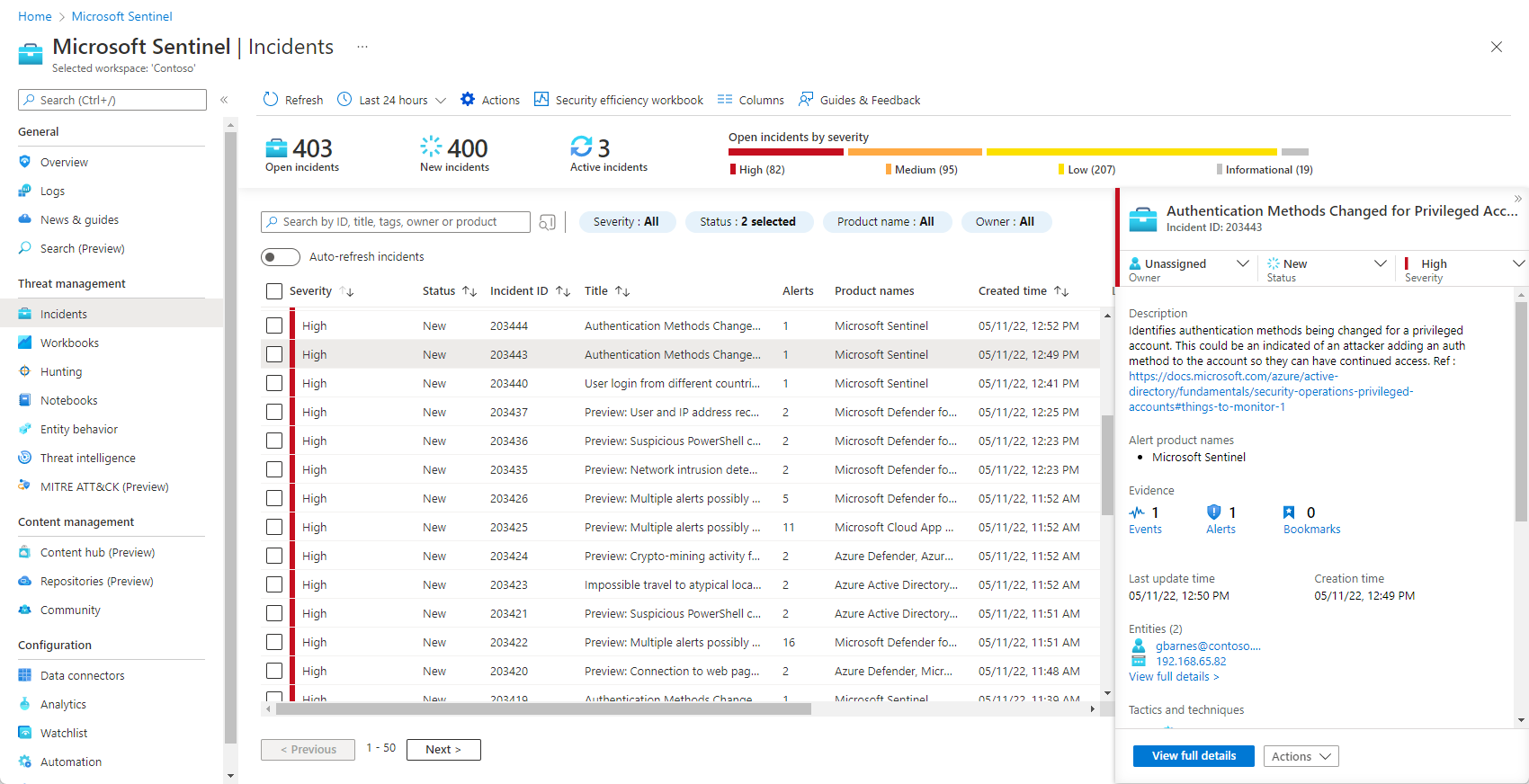
Incidents and investigation
An incident is created when an alert that you’ve enabled is triggered. In Microsoft Sentinel, you can do standard incident management tasks like changing status or assigning incidents to individuals for investigation. Microsoft Sentinel also has investigation functionality, so you can visually investigate incidents by mapping entities across log data along a timeline.
Automation playbooks
With the ability to respond to incidents automatically, you can automate some of your security operations and make your SOC more productive. Microsoft Sentinel allows you to create automated workflows, or playbooks, in response to events. This functionality could be used for incident management, enrichment, investigation, or remediation. These capabilities are often referred to as security orchestration, automation, and response (SOAR).
search in (CommonSecurityLog) “172.17.20.10”
search in (Syslog) “172.17.20.10”
CommonSecurityLog
| where DeviceVendor contains “Palo Alto Networks”
| where DeviceCustomString6 contains “LogForward”