Privilege Manager’s toolset is two-fold. First, Local Security discovers all accounts that exist on endpoints and allows Privilege Manager Administrators to control the exact membership of every local group. This will ensure the correct admin and root accounts are permanently set. Additionally, credentials will be controlled by enforcing password rotation on those accounts.
Second, Application Control allows Privilege Manager administrators to manage application activity on endpoint machines. Applications that require admin rights or root access can be automatically elevated, allowed applications are allow listed, and malicious applications are blocked.
Every implementation looks different when configuring Privilege Manager to work best for your organization. This post is to summarize some of examples to set up right policies in Privilege Manager application.
Related Post:
Best Practices
The following topics are available:
- Disaster Recovery
- Active Directory Import
- Using a Service Account to run the IIS App pool
- Prevent Read and Write Access to File Types or Locations
- Securing the IIS Server
- Updating to higher security algorithms
Notes:
Privilege Manager local accounts should be managed by Thycotic Secret Server.
License expired, the existing policies and new created policies will still wor, but not events.
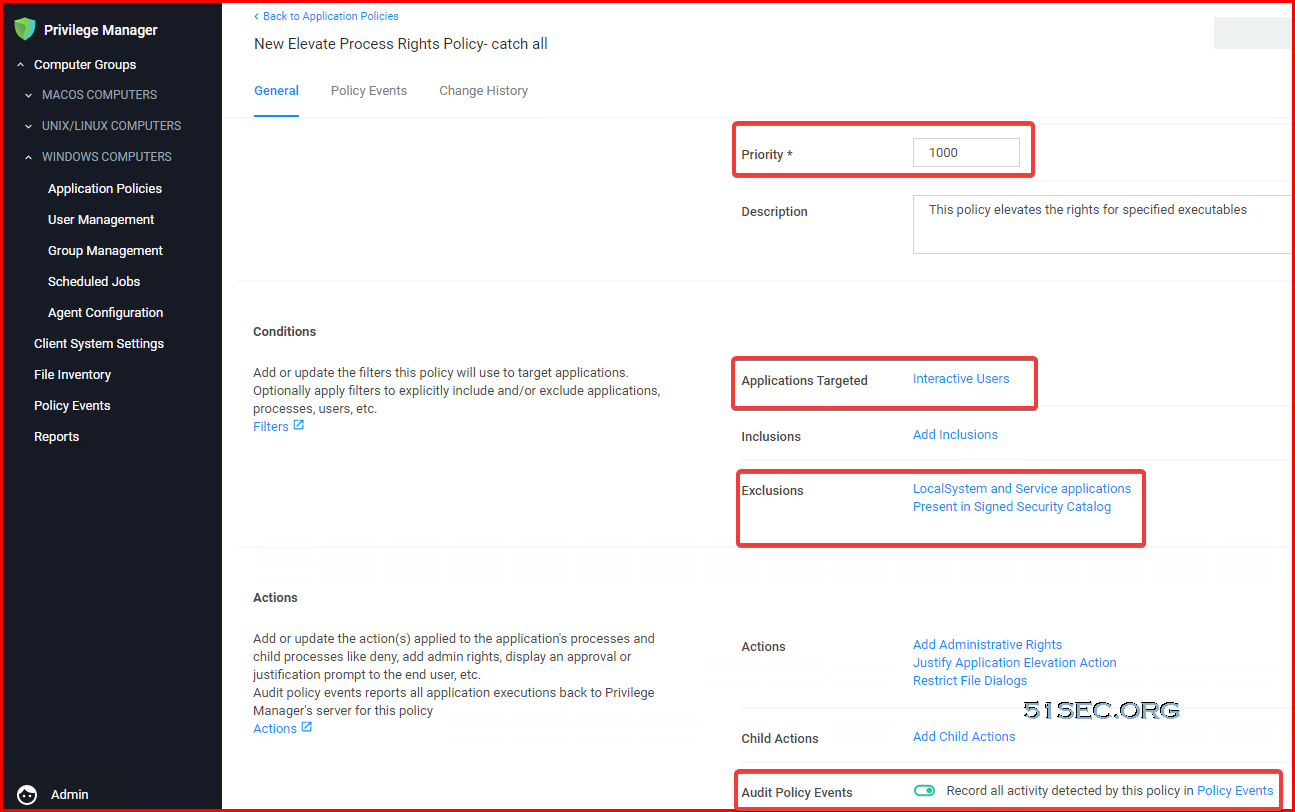
Catch All Policy
1. Monitoring policy
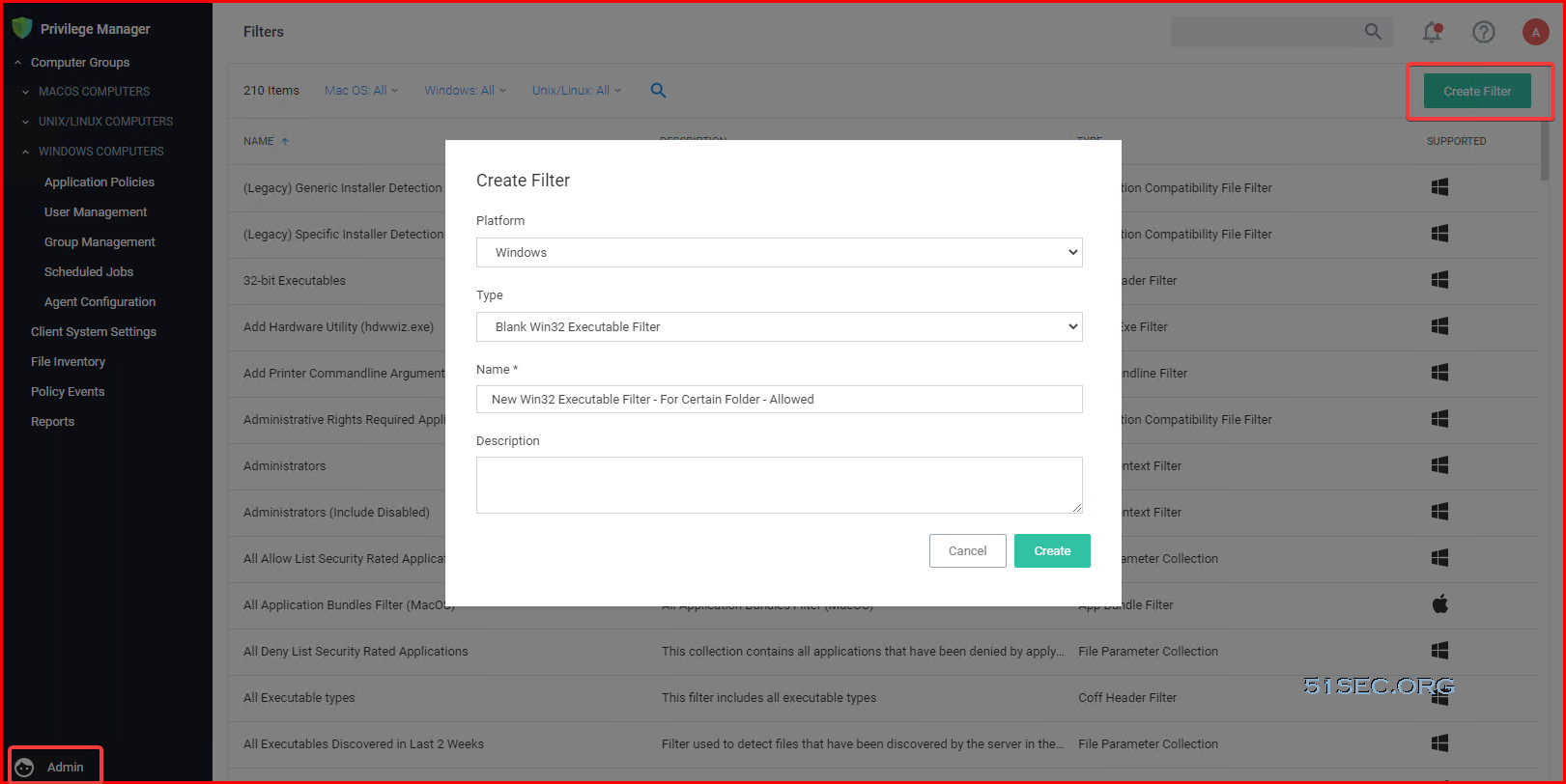
Custom Filter for Allowed Folder / Applications
To allow any application in certain folder to run, it requires to create a custom filter:
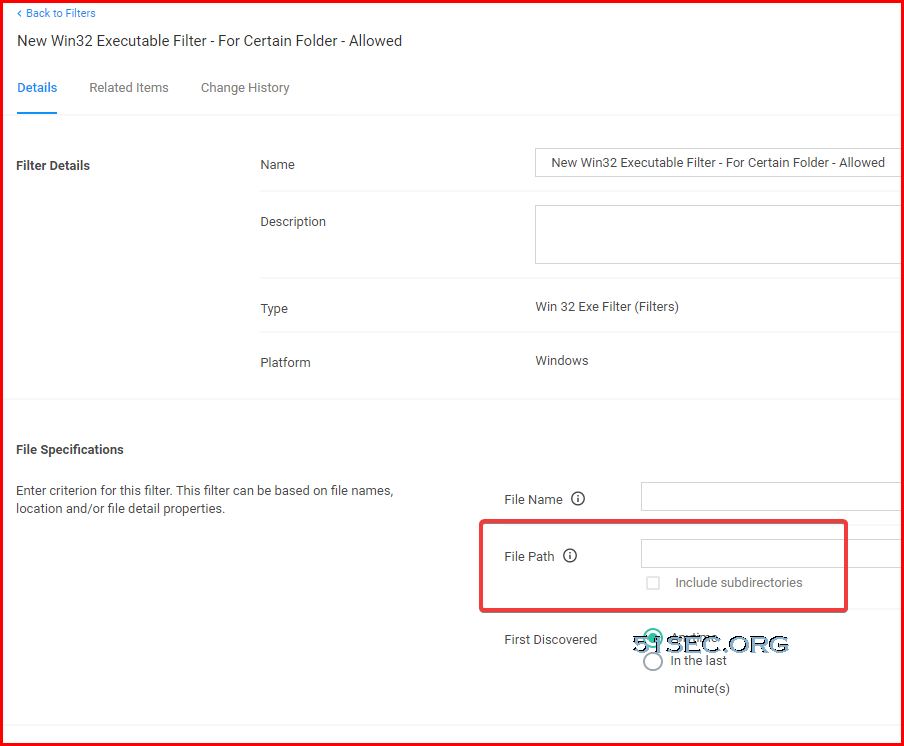
Enter folder location:
Then create an Allow policy:
- Setting up priority
- Change it to active
- Enable Auditing.
Set up Target Groups for your Policy
from Blogger http://blog.51sec.org/2021/09/thycotic-privilege-manager-basic.html