Still Under Writing…
 A Threat and Risk Assessment analyzes a software or hardware system for vulnerabilities, examines potential threats associated with those vulnerabilities, and evaluates the resulting security risks. A vulnerability is any “flaw or weakness in system security procedures, design, implementation, or internal controls that could be exercised (accidentally triggered or intentionally exploited) and result in a security breach or a violation of the system’s security policy” (NIST SP800-30 Risk Management Guide for Information Technology Systems). The level of threat is determined from the potential for any natural, human or environmental source to trigger or exploit any identified vulnerability. The risk assessment looks at both the probability of that threat occurring, and the impact on both system and organization should it occur. An appropriate strategy can then be formulated for each risk depending on severity (such as acceptance of the risk, adoption of a mitigation plan, or implementation of an avoidance strategy).
A Threat and Risk Assessment analyzes a software or hardware system for vulnerabilities, examines potential threats associated with those vulnerabilities, and evaluates the resulting security risks. A vulnerability is any “flaw or weakness in system security procedures, design, implementation, or internal controls that could be exercised (accidentally triggered or intentionally exploited) and result in a security breach or a violation of the system’s security policy” (NIST SP800-30 Risk Management Guide for Information Technology Systems). The level of threat is determined from the potential for any natural, human or environmental source to trigger or exploit any identified vulnerability. The risk assessment looks at both the probability of that threat occurring, and the impact on both system and organization should it occur. An appropriate strategy can then be formulated for each risk depending on severity (such as acceptance of the risk, adoption of a mitigation plan, or implementation of an avoidance strategy).
Define TRA Methodology
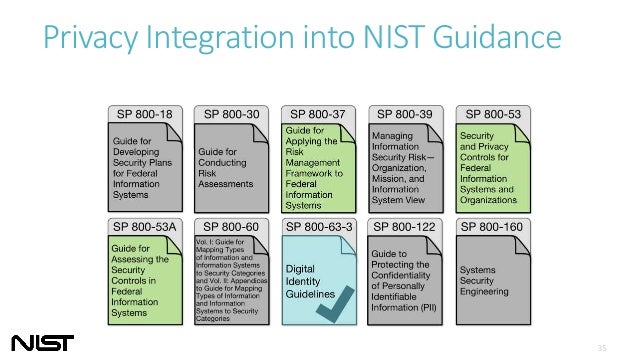
NIST
SP 800-30 Rev. 1 – Guide for Conducting Risk Assessments
FIPS 200 – Minimum Security Requirements for Federal Information and Information Systems
FIPS 199 – Standards for Security Categorization of Federal Information and Information Systems
Define Process
Based on FIPS 200, the generalized format for expressing the
security category (SC) of an information system is:
SC information system = {(confidentiality, impact), (integrity, impact), (availability, impact)},
where the acceptable values for potential impact are low, moderate, or high.
Since the potential impact values for confidentiality, integrity, and availability may not always be the
same for a particular information system, the high water mark concept must be used to determine the
overall impact level of the information system.
Define Scope
Organizations must meet the minimum security requirements in this standard by selecting the
appropriate security controls and assurance requirements as described in NIST Special Publication
800-53, Recommended Security Controls for Federal Information Systems
The selected set of security controls must include one of three, appropriately
tailored8
security control baselines from NIST Special Publication 800-53 that are associated with the
designated impact levels of the organizational information systems as determined during the security
categorization process.
– For low-impact information systems, organizations must, as a minimum, employ
appropriately tailored security controls from the low baseline of security controls defined in
NIST Special Publication 800-53 and must ensure that the minimum assurance requirements
associated with the low baseline are satisfied.
– For moderate-impact information systems, organizations must, as a minimum, employ
appropriately tailored security controls from the moderate baseline of security controls
defined in NIST Special Publication 800-53 and must ensure that the minimum assurance
requirements associated with the moderate baseline are satisfied.
– For high-impact information systems, organizations must, as a minimum, employ
appropriately tailored security controls from the high baseline of security controls defined in
NIST Special Publication 800-53 and must ensure that the minimum assurance requirements
associated with the high baseline are satisfied.
Output
| Category | Security Control |
Low | Moderate | High |
| Access Control | Administrator Multi Factor Authentication |
x | x | |
| Access Control | Centralized Authentication |
x | x | |
| Access Control | Machine Authentication |
x | x | |
| Access Control | Physical Security |
x | x | x |
| Access Control | Role-based Authentication / Least Privilege |
x | x | |
| Access Control | Separation of duties |
x | x | |
| Access Control | User Multi Factor Authentication |
x | ||
| Audit | Audit Data Review |
x | x | x |
| Audit | Login Audit |
x | x | x |
| Configuration Management | Configuration Change Control |
x | x | x |
| Configuration Management | Notification of changes |
x | ||
| Configuration Management | System Component Inventory |
x | x | x |
| Contingency Planning | Contingency Plan |
x | x | x |
| Contingency Planning | Disaster Recovery Site |
x | ||
| Contingency Planning | Offsite Backup |
x | x | |
| Contingency Planning | Onsite Backup |
x | x | x |
| Incident Response | Incident Response |
x | x | x |
| Media Protection | Secure Delete |
x | x | |
| Risk Assessment | Penetration Testing |
x | ||
| Risk Assessment | Vulnerability Management |
x | x | x |
| System and Communication Protection | Data Leak Protection (DLP) |
x | x | |
| System and Communication Protection | DoS Protection |
x | ||
| System and Communication Protection | Encryption at rest |
x | x | |
| System and Communication Protection | Encryption in transit |
x | x | x |
| System and Communication Protection | Isolation in multi-tenant environment |
x | x | |
| System and Communication Protection | Network Segregation |
x | ||
| System and Information Integrity | Antivirus/Antimalware | x | x | x |
| System and Information Integrity | File Integrity Monitoring |
x | x | |
| System and Information Integrity | Host IDS |
x | ||
| System and Information Integrity | Network IDS |
x | x | |
| System and Information Integrity | Patch Management |
x | x | x |
| System and Information Integrity | Priviledged Access Management |
x | ||
| System and Information Integrity | System Hardening |
x | x | x |
| System and Information Integrity | System Health Monitoring |
x | x | x |
| Training | Awareness and Training |
x | x | x |
Other Documents:
Canadian Centre for Cyber Security -Annex 3A – Security Control Catalogue (ITSG-33)